
Cloud Attack Surface Management(CASM): What is it? How does Strobes CASM help you with cloud security?
The cloud revolutionized how businesses operate, but with increased flexibility comes an expanded attack surface. Traditional security methods struggle to keep pace with the dynamic nature of cloud environments, making Cloud Attack Surface Management (CASM) a crucial tool for modern security teams.
In this blog, explore how Strobes CASM elevates cloud security to new heights-
What is Cloud Attack Surface Management?
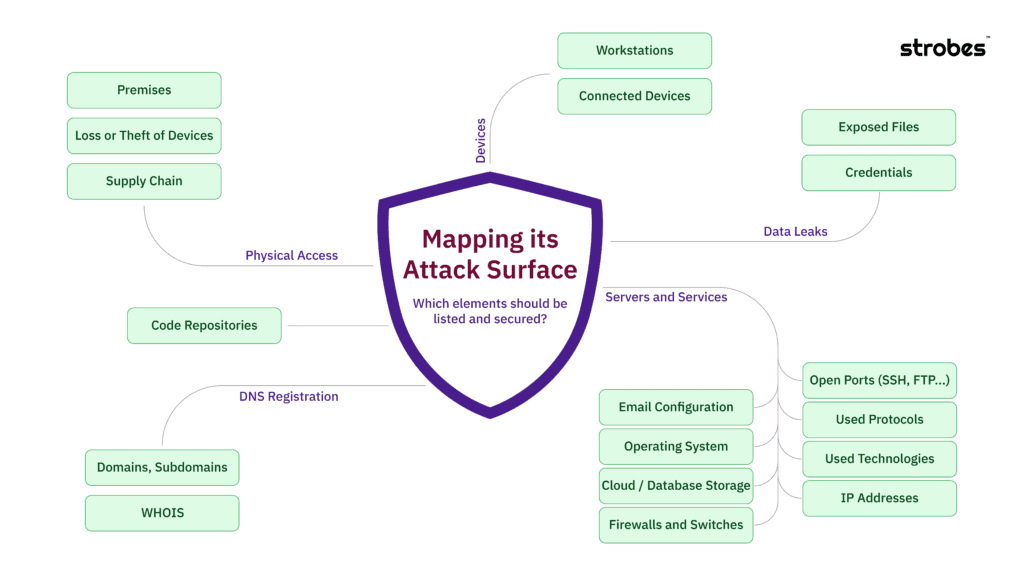
Cloud Attack Surface Management (CASM) encompasses a set of practices and technologies aimed at identifying, analyzing, and mitigating security risks within cloud environments.
At its core, CASM focuses on gaining visibility into all assets and potential vulnerabilities across cloud infrastructure, including Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) offerings.
One of the key challenges in cloud security is the discovery of assets beyond the known infrastructure. While traditional security tools may offer basic asset visibility, CASM solutions like Strobes go a step further by employing advanced discovery methods.
These methods uncover the often-neglected "dark areas" of the cloud environment, such as orphaned SaaS subscriptions, unmanaged API endpoints, and forgotten PaaS resources.
Top Features of CASM-
1. Asset Discovery:
Many CASM tools offer basic asset visibility, focusing on known infrastructure. Strobes goes beyond, employing advanced discovery methods to uncover the often-neglected "dark areas" of your cloud environment:
- Orphaned SaaS subscriptions: Unused subscriptions become forgotten vulnerabilities. Strobes identify them, helping you reclaim resources and eliminate potential attack vectors.
- Unmanaged API endpoints: Unsecured APIs are open invitations for attackers. Strobes detects and flags them, allowing you to secure sensitive data and functionality.
- Forgotten PaaS resources: Gain valuable insights by enriching discovered assets with metadata from various sources, including CSP metadata, vulnerability databases, and threat intelligence feeds, enabling informed risk prioritization.
2. Visualizing Risk: From Chaos to Clarity:
Asset lists can overwhelm you. Strobes tackles this challenge with intelligent attack surface graphs that:
- Threat-centric attack graphs: Identify critical relationships between assets, visualize potential attack paths, and understand how vulnerabilities could be exploited.
- Interactive graph manipulation: Drill down into specific connections, filter based on risk factors, and gain a dynamic understanding of your attack surface's security posture.
- Customizable risk scoring: Leverage customizable scoring algorithms that factor in asset criticality, exploitability, and threat intelligence to prioritize critical vulnerabilities and optimise remediation efforts.
3. Risk-Based Prioritization for Security Teams:
Alert fatigue plagues many security teams. Strobes differentiates itself with risk-based monitoring that:
- Contextualizes alerts: Go beyond "new" notifications. Each alert is enriched with asset context, vulnerability severity, exploitability details, and threat intelligence, allowing you to understand the true risk and prioritize accordingly.
- Machine learning-powered threat correlation: Leverage machine learning algorithms to correlate seemingly disparate alerts, uncovering hidden attack campaigns and reducing false positives.
- Customizable alerting rules: Tailor your alerting notifications to your specific needs and threat profile, ensuring you receive essential information without being overwhelmed by noise.
Why do you need a CASM Software?
Cloud Attack Surface Management (CASM) is increasingly recognized as a critical component of a robust cybersecurity strategy in today's cloud-driven landscape. Here's why organizations need CASM:
- Expanded Attack Surface: With the widespread adoption of cloud computing, organizations are leveraging diverse cloud services, platforms, and infrastructure.
This expansion leads to a broader attack surface, increasing the potential entry points for cyber threats. CASM helps in comprehensively identifying and managing these attack surfaces, including assets that may be overlooked or forgotten.
- Dynamic Nature of Cloud Environments: Cloud environments are highly dynamic, with resources being provisioned, modified, and decommissioned rapidly. Traditional security approaches often struggle to keep pace with these changes, leading to gaps in security coverage. CASM solutions offer real-time visibility into the evolving cloud infrastructure, enabling proactive risk management and threat detection.
- Complexity of Cloud Infrastructure: Modern cloud infrastructures are complex, comprising multiple layers, services, and dependencies. This complexity introduces challenges in asset management, vulnerability assessment, and risk prioritization.
CASM tools provide organizations with the ability to visualize and understand their cloud environment holistically, facilitating informed decision-making and resource allocation.
- Compliance and Regulatory Requirements: Many industries are subject to stringent regulatory requirements concerning data protection and privacy. Cloud environments must adhere to these regulations, necessitating robust security measures and comprehensive risk management practices.
CASM solutions help organizations maintain compliance by identifying security gaps, prioritizing remediation efforts, and providing audit trails for regulatory purposes.
- Threat Landscape Evolution: Cyber threats are constantly evolving, with attackers employing sophisticated techniques to infiltrate cloud environments and exfiltrate sensitive data. CASM solutions leverage threat intelligence feeds, machine learning algorithms, and advanced analytics to detect emerging threats, correlate security events, and mitigate risks effectively. By staying ahead of the evolving threat landscape, organizations can enhance their cyber resilience and protect their digital assets.
- Risk Mitigation and Business Continuity: The consequences of security breaches in cloud environments can be severe, ranging from financial losses and reputational damage to legal liabilities and operational disruptions.
CASM enables organizations to proactively identify and mitigate security risks, reducing the likelihood and impact of potential cyber incidents. By safeguarding critical assets and ensuring business continuity, CASM contributes to the overall resilience of the organisation.
The Strobes Advantage: More Than Just Features
Strobes CASM offers a compelling combination of advanced discovery, insightful visualisation, and intelligent monitoring. But the benefits extend beyond technical features:
- Reduced risk: Mitigate the ever-present threat of cloud attacks by proactively addressing vulnerabilities.
- Improved decision-making: Gain actionable insights to prioritise security efforts and allocate resources effectively.
- Enhanced compliance: Meet regulatory requirements with confidence by maintaining a secure cloud environment.
- Peace of mind: Focus on your business goals knowing your cloud environment is actively protected.
Conclusion: Taking Control of Your Cloud Security
In today's cloud-driven world, a reactive approach to security is a recipe for disaster. Strobes CASM empowers you to proactively manage your attack surface, gain invaluable insights, and make informed decisions. By going beyond basic asset listing and offering intelligent risk management, Strobes gives you the power to secure your cloud and confidently navigate the ever-evolving threat landscape.
Ready to explore Strobes CASM in more detail? Contact us today for a personalised demo and see how we can help you take control of your cloud security.
Related Reads:
- Solution: Attack Surface Management
- Attack Surface Management: What is it? Why do you need it?
- Understanding External Attack Surface Management (EASM)
- Integrating Attack Surface Management and Penetration Testing as a Service
- How Strobes Uncover Hidden Cloud Risks Within Your Organization?
- Use Case: Rapid Identification and Escalation of a Critical Threat by Strobes ASM