With new threats emerging and existing ones becoming more sophisticated, cybersecurity is no longer a quiet backroom concern. Failure to prioritize cybersecurity leaves businesses, governments, and individuals vulnerable to crippling attacks with far-reaching consequences. To stay ahead of the curve, you need to partner with the right companies that are innovating and pushing the boundaries of security. That’s why we have created a list of top cybersecurity companies in the USA to watch in 2024.
The Cost of Neglect:
Cybersecurity breaches are no longer just an inconvenience. They’re financial sinkholes:
- The average cost of a data breach in 2023 is $4.45 million.
- Ransomware attacks spiked by over 37% in 2023, with the average enterprise ransom exceeding $100,000. Some even faced jaw-dropping demands of $5.3 million.
- Email-based phishing attacks have surged a whopping 464% in the first half of 2023.
Finding the Right Partner Matters:
From ransomware to nation-state espionage, the threats are diverse. Your partner needs the experience to anticipate every attack and the agility to deploy countermeasures on the fly. The right cybersecurity firms in the USA bring:
- Expertise: Deep understanding of the threat landscape, vulnerabilities, and evolving tactics.
- Technology: Cutting-edge solutions for endpoint protection, network security, threat intelligence, and incident response.
- Proactive Approach: Continuous monitoring, analysis, and adaptation to stay ahead of the curve.
- Scalability: Solutions tailored to your specific needs and growth.
Now, without further ado, here are the top cybersecurity companies in the USA to watch in 2024.
Top Cybersecurity Companies in the USA
- Strobes
- Palo Alto Networks
- WeSecureApp
- Microsoft
- Fortinet
- Cisco
- IBM Security
- Okta
- Sophos
- SentinelOne
- Crowdstrike
- Tenable
- Rapid7
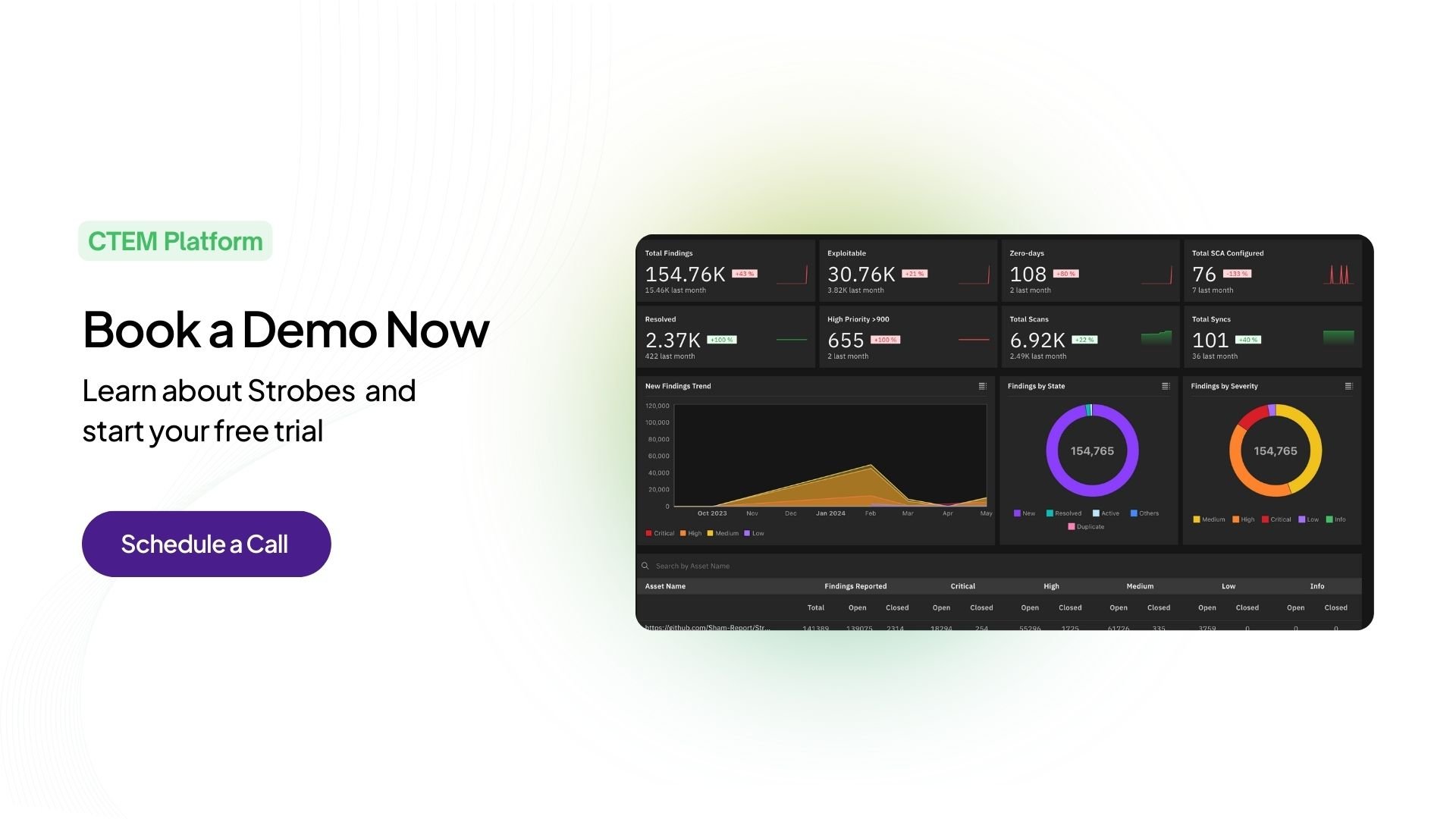
1. Strobes
Company Overview: Founded in 2019, Strobes is a rapidly growing cybersecurity innovator, empowering organizations of all sizes with cutting-edge security solutions. We prioritize flexibility, tailoring the expertise to meet the unique needs of enterprises, SMBs, and across various industries.
Specialties: Strobes shines in its mastery of cutting-edge technologies. Their flagship offerings include:
- Attack Surface Management (ASM): Continuously map and monitor your external attack surface, identifying vulnerabilities before attackers do.
- Penetration Testing as a Service (PTaaS): Simulated cyberattacks conducted by the expert pentesting team, uncovering exploitable weaknesses in your security.
- Risk-Based Vulnerability Management (RBVM): Prioritize and remediate vulnerabilities based on real-time exploitability and business impact.
- Continuous Threat Exposure Management (CTEM): Centralize security data, detect threats in real-time, and orchestrate response across your ecosystem.
Key Differentiators: Strobes stands apart through its:
- Fusion of automation and human expertise: Their solutions combine powerful AI-driven tools with the critical insights of experienced security professionals.
- Client-centric approach: Strobes collaborates closely with clients to understand their unique needs and tailor solutions that fit their specific risk landscape.
- Focus on continuous improvement: Constant innovation and adaptation to the ever-changing threat landscape are hallmarks of Strobes philosophy.
Target Audience: Strobes caters to organizations of all sizes with complex IT infrastructures, particularly those operating in high-risk industries. Their solutions are ideal for organizations seeking proactive, data-driven security strategies.
2. Palo Alto Networks
Company Overview: Palo Alto Networks is a cybersecurity behemoth, established in 2005, renowned for its Next-Generation Firewalls (NGFWs) and comprehensive security suite. They cater primarily to large enterprises and government agencies.
Specialties: Palo Alto Networks’ core strengths lie in:
- Next-Generation Firewalls: Their NGFWs offer advanced threat detection and prevention capabilities, including deep packet inspection and application identification.
- Cloud Security: They provide cloud-native security solutions for protecting workloads across public, private, and hybrid cloud environments.
- Endpoint Security: Their endpoint protection solutions offer a comprehensive defense against malware, ransomware, and other targeted attacks.
Key Differentiators: Palo Alto Networks stands out through its:
- Established Brand: Their large market share and established reputation make them a trusted choice for large organizations.
- Broad Product Portfolio: They offer a wide range of security solutions, catering to a diverse set of security needs.
- Proven Track Record: They have a long history of success in protecting large enterprises from sophisticated cyberattacks.
Target Audience: Palo Alto Networks primarily targets large enterprises and government agencies with complex security needs and substantial budgets.
3. WeSecureApp
Company Overview: WeSecureApp is a rapidly growing Indian cybersecurity company, founded in 2013, specializing in offensive security solutions including, application, cloud, and network penetration testing. WeSecureApp’s agility and focus on developer experience set them apart. Their cloud-based platform makes security accessible and easy to implement, even for organizations with limited security resources. Their unique blend of automated tools and human expertise provides a comprehensive and cost-effective approach to application security.
Specialties: WeSecureApp’s core strengths lie in:
- Application Security: They offer comprehensive security assessments for web and mobile applications, identifying vulnerabilities and recommending remediation strategies.
- Penetration Testing: Their skilled ethical hackers perform in-depth penetration tests to uncover security weaknesses and simulate real-world attacks.
- Cloud Security: They provide expertise in securing cloud environments, including infrastructure, applications, and data.
Key Differentiators: WeSecureApp stands out through their:
- Focus on Application Security: They have a deep understanding of web and mobile application security, making them a valuable partner for organizations with digital assets.
- Cost-Effective Solutions: They offer competitive pricing, making their services accessible to SMBs and mid-sized businesses with limited budgets.
Target Audience: Organizations of all sizes, particularly those developing and deploying web and mobile applications, who value personalized service and a consultative approach to application security.
4. Microsoft
Company Overview: A global tech behemoth, Microsoft has leveraged its vast resources to become a cybersecurity powerhouse. With over 220,000 employees and a focus on cloud-based solutions, Microsoft caters primarily to enterprise clients across various industries.
Specialties: Microsoft boasts a diverse suite of offerings, including Azure Sentinel (SIEM), Defender for Endpoint (EDR), and Azure Active Directory (identity management). Their strength lies in cloud-native security architecture, scalability, and integration with other Microsoft products.
Key Differentiators: Microsoft excels in leveraging its extensive cloud infrastructure and AI capabilities to deliver proactive threat detection and response. Additionally, their deep integration with existing Microsoft ecosystems provides seamless security for organizations already invested in the platform.
Target Audience: Enterprise organizations looking for a comprehensive, cloud-based security solution with seamless integration into existing Microsoft environments.
5. Fortinet
Company Overview: Founded in 2006, Fortinet has rapidly climbed the cybersecurity ladder, becoming a major player with over 12,000 employees. Their focus lies on integrated security appliances and platforms, catering to a broad range of clients from SMBs to large enterprises.
Specialties: Fortinet’s forte lies in its Security Fabric, a unified platform encompassing firewalls, intrusion prevention, sandboxing, and endpoint protection. They prioritize integrated, all-in-one solutions with simplified management and visibility.
Key Differentiators: Fortinet’s commitment to an integrated approach, coupled with its broad product portfolio and competitive pricing, sets it apart. They offer a compelling option for organizations seeking a one-stop shop for their security needs.
Target Audience: SMBs and enterprises seeking an integrated security platform with simplified management and a cost-effective approach.
6. Cisco
Company Overview: A networking giant with a rich history, Cisco has expanded its reach into cybersecurity through strategic acquisitions and organic development. With over 80,000 employees, they cater to a wide range of clients across all industries.
Specialties: Cisco excels in network security solutions, including firewalls, intrusion detection and prevention systems, and secure access control. They emphasize visibility and control over network traffic, along with integration with other Cisco networking products.
Key Differentiators: Cisco’s strength lies in its extensive network expertise and ability to provide comprehensive network-based security solutions. Their focus on integration and collaboration within existing network environments makes them a valuable partner for organizations heavily invested in Cisco technology.
Target Audience: Enterprises with complex network infrastructures seeking robust network security solutions and seamless integration with existing Cisco products.
7. IBM Security
Company Overview: A tech giant since 1911, IBM Security boasts a rich history of innovation, acquiring numerous security firms over the years to build a comprehensive portfolio. Their size and global reach make them a dominant force in enterprise security, catering to large organizations across various industries.
Specialties: IBM Security excels in X-Force threat intelligence, security information and event management (SIEM), and cloud security solutions. Their QRadar SIEM platform is a popular choice for large enterprises, while their cloud security offerings integrate seamlessly with major cloud providers.
Key Differentiators: IBM’s sheer size and resources allow them to invest heavily in research and development, constantly pushing the boundaries of security technology. Their focus on AI and machine learning-powered solutions helps them stay ahead of the curve in threat detection and prevention.
Target Audience: Primarily large enterprises and government agencies with complex security needs and budgets to match.
8. Okta
Company Overview: Founded in 2009, Okta is a relative newcomer compared to IBM but has quickly become a leader in identity and access management (IAM). Their focus on cloud-based solutions and user-friendly interfaces has made them a favorite among businesses of all sizes.
Specialties: Okta’s core strength lies in its comprehensive IAM platform, which simplifies user authentication and access control across various applications and cloud services. Their single sign-on (SSO) technology eliminates the need for juggling multiple logins, improving both security and user experience.
Key Differentiators: Okta’s cloud-native approach and API-driven architecture make it highly scalable and adaptable to diverse IT environments. Their focus on user experience and ease of integration has earned them a loyal following among businesses seeking a streamlined approach to identity management.
Target Audience: Businesses of all sizes, particularly those with cloud-based applications and a focus on user-centric security.
9. Sophos
Company Overview: Founded in 1983, Sophos is a veteran in the cybersecurity space, initially known for its antivirus software. Today, they offer a wide range of security solutions for businesses of all sizes, with a strong focus on endpoint protection and synchronized security.
Specialties: Sophos’s core strength lies in its synchronized security approach, which combines endpoint protection, network security, and cloud security into a single platform. This integrated approach simplifies security management and provides comprehensive protection against modern threats.
Key Differentiators: Sophos’s focus on synchronized security and ease of use makes them a popular choice for small and medium-sized businesses (SMBs) seeking an all-in-one security solution. Their competitive pricing and flexible deployment options further enhance their appeal.
Target Audience: SMBs and enterprises seeking a comprehensive and affordable security solution with a focus on ease of use and management.
10. SentinelOne
Company Overview: Founded in 2013, SentinelOne is a rising star in the cybersecurity world, known for its innovative approach to endpoint protection. Their focus on behavioral analysis and machine learning helps them detect and prevent even the most sophisticated cyberattacks.
Specialties: SentinelOne’s core strength lies in its Singularity XDR platform, which combines endpoint protection, endpoint detection and response (EDR), and incident response capabilities into a single solution. This unified approach provides real-time threat visibility and rapid response to security incidents.
Key Differentiators: SentinelOne’s use of machine learning and behavioral analysis makes it highly effective in detecting and preventing zero-day attacks and advanced threats. Their cloud-based architecture and proactive approach to security make them a compelling choice for organizations looking for cutting-edge endpoint protection.
Target Audience: Enterprises and organizations with high-value assets and a need for advanced endpoint protection against sophisticated cyberattacks.
11. CrowdStrike
Company Overview: Founded in 2011, CrowdStrike has become a cybersecurity titan, powering endpoint protection and threat intelligence for enterprises across diverse industries. Their global reach and proven track record make them a force to be reckoned with.
Specialties: CrowdStrike’s bread and butter lies in endpoint security (EDR, XDR), incident response, and threat intelligence. Their Falcon platform provides comprehensive endpoint visibility and proactive threat hunting, making them a popular choice for large-scale organizations.
Key Differentiators: CrowdStrike boasts an impressive cloud-native architecture, a global threat intelligence network, and robust incident response capabilities. Their aggressive threat-hunting approach and focus on real-time detection resonate with organizations facing high-stakes security challenges.
Target Audience: Their solutions cater primarily to large enterprises with complex IT environments and demanding security needs. Their expertise in incident response and threat intelligence makes them ideal for organizations navigating high-risk landscapes.
12. Tenable
Company Overview: Established in 2004, Tenable has carved a niche in the vulnerability management space. Their focus on continuous vulnerability assessment and prioritization makes them a go-to choice for organizations seeking proactive threat mitigation.
Specialties: Tenable’s forte lies in vulnerability management, compliance, and attack surface management. Their Nessus platform offers comprehensive scans, prioritized remediation recommendations, and real-time vulnerability tracking, ensuring organizations stay ahead of potential security vulnerabilities.
Key Differentiators: They focus on vulnerability prioritization and integration with security orchestration and response (SOAR) platforms sets them apart. Their ability to streamline vulnerability management processes and provide actionable insights makes them a valuable asset for organizations seeking to optimize their security posture.
Target Audience: Tenable solutions cater to organizations of all sizes, particularly those with complex IT infrastructures and a need for robust vulnerability management strategies. Their scalable solutions and industry-specific compliance tools make them a versatile option for diverse security needs.
13. Rapid7
Company Overview: Founded in 2000, Rapid7 has carved a path in the realm of security information and event management (SIEM) and vulnerability management. Their focus on security analytics and automation makes them a popular choice for organizations seeking to optimize their security operations.
Specialties: Their core strengths lie in SIEM, incident response, and vulnerability management. Their Insight platform provides real-time threat detection, log management, and incident response capabilities, enabling organizations to gain insights and respond to threats effectively.
Key Differentiators: Rapid7’s cloud-based SIEM solution and focus on automation through SOAR integrations set them apart. Their ability to leverage security data for actionable insights and automate security workflows makes them a valuable asset for organizations seeking to streamline their security operations.
Target Audience: Rapid7’s solutions cater to organizations of all sizes, particularly those seeking to improve their security analytics and automation capabilities. Their user-friendly platform and broad range of security tools make them a versatile option for diverse security needs.
| Company Name | Overviews | Specialities | Differentiators | Target Audience |
| Strobes | Founded in 2019, dynamic growth, and global reach. | ASM, PTaaS, RBVM, CTEM expertise. | Fusion of automation and human expertise, Client-centric approach | SMBs and enterprises of all sizes. |
| Palo Alto Networks | Established in 2005, cybersecurity giant. | NGFWs, Cloud Security, Endpoint Security. | Established brand and broad product portfolio. | Large enterprises, government agencies |
| WeSecureApp | Founded in 2013, agile cybersecurity company. | Application Security, Penetration Testing. | Focus on application security, Cost-effective solutions | Organizations of all sizes, app development. |
| Microsoft | Global tech behemoth, cloud focus. | Cloud-based solutions, AI capabilities. | Cloud-based solutions, Extensive cloud infrastructure. | Enterprise organizations with complex IT environments. |
| Fortinet | Founded in 2006, integrated security. | Security Fabric, Integrated solutions. | The integrated approach is a broad product portfolio. | SMBs and enterprises. |
| CISCO | Networking giant, extensive reach. | Network security, Firewalls, Access control. | Extensive network expertise and comprehensive network-based solutions. | Enterprises with complex network infrastructures. |
| IBM | Tech giant since 1911, global presence. | SIEM, X-Force Cloud Security. | Size and resources, AI and ML focus. | Large enterprises, and government agencies. |
| Okta | Founded in 2009, IAM leader. | IAM, SSO, User-friendly interfaces. | Cloud-native approach, API-driven architecture. | Businesses of all sizes. |
| SOPHOS | Veteran since 1983, wide range. | Synchronized Security, Endpoint focus. | Focus on synchronized security | SMBs and enterprises |
| SentinelOne | Since 2013, innovative endpoint. | Singularity XDR, Behavioral analysis. | Machine learning, Behavioral analysis. | Enterprises and organizations with high-value assets. |
| Crowdstrike | Founded in 2011, Global reach and proven track record. | Endpoint security, incident response, and threat intelligence. | Cloud-native architecture, global threat intelligence network. | Large enterprises with complex IT environments. |
| Tenable | Established in 2004, vulnerability expert. | Vulnerability management, compliance. | Vulnerability prioritization, SOAR integration. | Organizations of all sizes with complex IT infrastructures. |
| Rapid7 | Founded in 2000, SIEM and VM specialist. | SIEM, incident response, VM. | Cloud-based SIEM, automation. | Organizations of all sizes, have an emphasis on analytics and automation. |
Key Takeaways
The cybersecurity industry is rapidly changing, demanding proactive and innovative solutions. Choosing the right partner is crucial for securing your organization in 2024. Strobes stands out with its focus on threat detection, unique methodologies, and proven success in protecting businesses of all sizes.