Vulnerability assessment is a process that identifies security weaknesses of any IT system, network, application, or cloud environment. It is a proactive approach to detect and fix security gaps before any cyber criminals exploit them.
Think of it like a security health check for your digital assets. Similar to a medical examination, it proactively scans computers, servers, websites, and databases to discover vulnerabilities that attackers could use to gain unauthorized access or cause harm.
Vulnerability assessments utilize automated scanning tools along with manual methods to detect issues such as misconfigured systems, outdated software, weak passwords, and security loopholes. After identifying vulnerabilities, security professionals analyze and rank them according to risk severity.
Conducting regular vulnerability assessments enables organizations to enhance cybersecurity, reduce the risk of cyberattacks, protect sensitive data, and maintain compliance with industry security standards.
Why Organizations Need to Conduct Regular Vulnerability Assessments?
Cyber threats evolve every day. Attackers constantly look for weaknesses in systems, and even a small vulnerability can lead to a major security breaches. Regular vulnerability assessments help organizations stay ahead of these threats by identifying and fixing security gaps before hackers can exploit them.
Meet Compliance and Regulatory Requirements
Regulations like PCI-DSS, HIPAA, and ISO 27001 require organizations to perform regular vulnerability assessments. Failing to comply can result in fines, legal issues, and loss of business contracts. Routine security assessments help maintain security compliance, audit readiness, and avoid penalties.
Reduce the Risk of Cyberattacks
New vulnerabilities emerge as software, networks, and applications are updated. Without frequent assessments, organizations remain unaware of security flaws that attackers can use to gain access. Regular scans detect misconfigurations, weak passwords, and unpatched software, reducing the chance of a data breach or ransomware attack.
Protect Sensitive Data and Business Operations
A single exploited vulnerability can expose customer records, financial data, or intellectual property. Cybercriminals target critical information, leading to financial losses, reputational damage, and regulatory penalties. Regular assessments ensure data protection by identifying security weaknesses before they become entry points for attackers.
Prioritize and Fix Critical Vulnerabilities
Not all vulnerabilities pose the same risk. A low-severity bug in an internal system is less dangerous than an unpatched internet-facing server. Regular assessments use risk-based prioritization to focus on fixing the most critical vulnerabilities first, ensuring that security teams spend time on the biggest threats.
Strengthen Incident Response and Security Posture
When an attack happens, organizations must respond quickly. A well-executed vulnerability assessment program improves incident response by ensuring that systems are hardened against known threats. It also provides visibility into the attack surface, helping security teams proactively strengthen defenses before an attack occurs.
How Vulnerability Assessment Differs from Penetration Testing?
Aspect | Vulnerability Assessment | Penetration Testing |
| Definition | A process to identify, analyze, and prioritize security weaknesses in a system. | A simulated cyberattack to exploit vulnerabilities and test system defenses. |
| Purpose | To detect and list security flaws before attackers find them. | To check how an attacker can exploit vulnerabilities and how deep they can go. |
| Approach | Passive; only identifies and analyzes vulnerabilities. | Active; exploits vulnerabilities like a real hacker. |
| Scope | Broad; covers entire IT infrastructure (network, applications, cloud, etc.). | Focused; targets specific systems to test real-world attack scenarios. |
| Tools Used | Automated scanners like Nessus, OpenVAS, Qualys, Burp Suite. | Manual techniques + tools like Metasploit, Kali Linux, Core Impact. |
| Execution | Usually automated, with some manual verification. | Mostly manual, with skilled ethical hackers performing real attacks. |
| Risk Analysis | Assigns severity scores (like CVSS) to each vulnerability. | Shows actual business impact of exploited vulnerabilities. |
| Impact on System | Low; does not affect system functionality. | Medium to High; can disrupt services if not done carefully. |
| Time Required | Faster; can be completed in a few hours to days. | Slower; can take days to weeks for a full test. |
| Frequency | Performed regularly (weekly, monthly, or quarterly). | Conducted periodically (e.g., annually or after major changes). |
| Cost | Generally less expensive due to automation. | More costly as it requires expert ethical hackers. |
| Compliance Requirements | Vulnerability assessments are mandatory for compliance standards like ISO 27001, PCI-DSS, HIPAA, GDPR. | Penetration testing is mandatory for standards like PCI-DSS (Requirement 11.3) and is strongly recommended in NIST, ISO 27001, and SOC 2 for high-risk environments. |
| End Result | A list of security weaknesses with risk ratings. | A detailed report on exploited vulnerabilities and security improvements needed. |
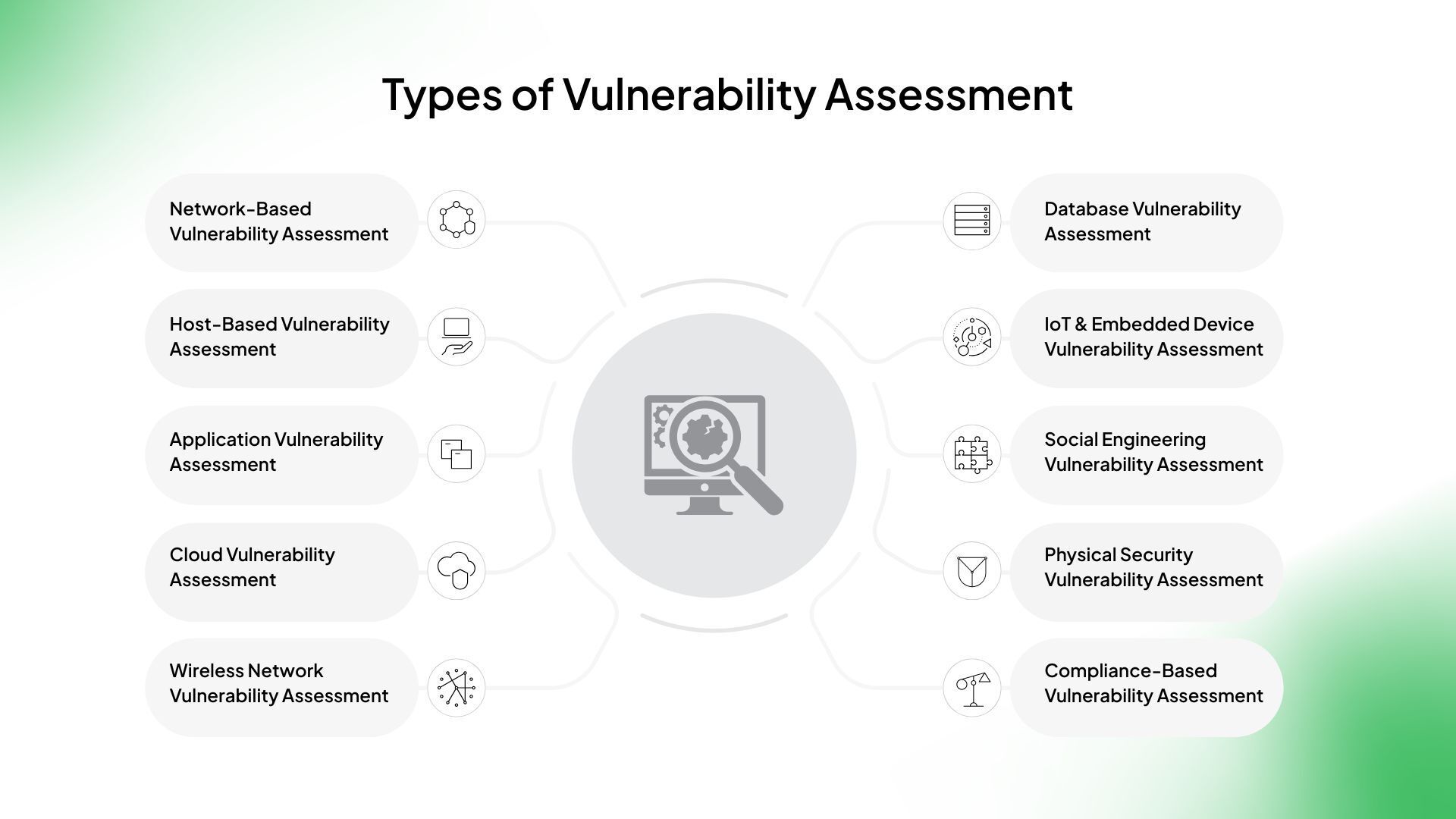
Types of Vulnerability Assessment
 1. Network-Based Vulnerability Assessment
1. Network-Based Vulnerability Assessment
- Scans internal and external networks for vulnerabilities.
- Identifies misconfigurations, open ports, weak authentication, and outdated software.
- Helps protect firewalls, routers, switches, and network servers.
Solution: Network Security
2. Host-Based Vulnerability Assessment
- Focuses on individual servers, workstations, and endpoints.
- Scans for OS weaknesses, unpatched software, and improper configurations.
- Helps organizations secure critical assets like databases and application servers.
3. Application Vulnerability Assessment
- Targets web and mobile applications for security flaws.
- Identifies SQL injection, cross-site scripting (XSS), authentication bypass, and insecure APIs.
- Includes Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST).
Solution: Application Security
4. Cloud Vulnerability Assessment
- Assesses cloud infrastructure, storage, and virtual machines.
- Identifies misconfigured cloud services, exposed credentials, and weak IAM policies.
- Ensures compliance with CIS benchmarks, NIST, and ISO standards.
Solution: Cloud Security
5. Wireless Network Vulnerability Assessment
- Identifies weaknesses in Wi-Fi networks, access points, and wireless protocols.
- Detects rogue access points, weak encryption (WEP, WPA), and SSID exposure.
- Ensures network segmentation and protection from man-in-the-middle (MITM) attacks.
6. Database Vulnerability Assessment
- Scans databases (SQL, NoSQL, Oracle, MySQL, etc.) for security flaws.
- Identifies default credentials, misconfigurations, SQL injection risks, and unauthorized access.
- Helps protect sensitive customer and business data.
7. IoT & Embedded Device Vulnerability Assessment
- Focuses on smart devices, industrial control systems (ICS), and medical devices.
- Identifies firmware vulnerabilities, weak authentication, and exposed communication protocols.
- Helps secure critical infrastructure and connected devices.
8. Social Engineering Vulnerability Assessment
- Tests how employees respond to phishing, vishing (voice phishing), and impersonation attacks.
- Helps organizations assess human weaknesses in security awareness.
- Involves simulated phishing campaigns and security training exercises.
9. Physical Security Vulnerability Assessment
- Assesses building security, access control systems, and surveillance.
- Identifies risks of unauthorized access, tailgating, or lack of CCTV coverage.
- Ensures compliance with physical security policies.
10. Compliance-Based Vulnerability Assessment
- Ensures adherence to industry standards like ISO 27001, HIPAA, PCI-DSS, NIST, and GDPR.
- Helps organizations meet regulatory requirements and avoid penalties.
- Focuses on security gaps related to data protection and risk management.
Also Read: What is Vulnerability Management? Compliance, Challenges, & Solutions
What Threats Can Be Avoided by Vulnerability Assessments?
Vulnerability assessments help organizations identify and fix security weaknesses before attackers can exploit them. Here are some major threats that can be avoided with regular vulnerability assessments:
1. Malware & Ransomware Attacks
- Identifies unpatched software and misconfigurations that malware can exploit.
- Prevents ransomware by detecting weak authentication and unsecured remote access.
- Helps organizations strengthen endpoint security and implement proper patching policies.
2. Data Breaches & Leaks
- Scans for exposed databases, misconfigured cloud storage, and weak encryption.
- Prevents sensitive data (customer records, financial info, PII) from being stolen.
- Ensures strong access controls and proper data protection.
3. Unauthorized Access & Privilege Escalation
- Detects weak passwords, default credentials, and lack of multi-factor authentication (MFA).
- Prevents hackers from gaining unauthorized access to critical systems.
- Helps organizations implement least privilege access (Zero Trust approach).
4. Phishing & Social Engineering Attacks
- Identifies weaknesses in email security settings (DMARC, SPF, DKIM).
- Helps organizations train employees to recognize and report phishing attempts.
- Strengthens identity verification processes to prevent impersonation attacks.
5. Denial-of-Service (DoS) & Distributed Denial-of-Service (DDoS) Attacks
- Detects unpatched vulnerabilities in web applications and network devices.
- Identifies misconfigured firewalls, load balancers, and rate-limiting settings.
- Helps organizations implement DDoS protection strategies.
6. Web Application & API Attacks
- Finds SQL injection, cross-site scripting (XSS), broken authentication, and API vulnerabilities.
- Helps developers fix insecure coding practices before applications go live.
- Ensures secure API authentication and encryption.
Solution: API Pentesting
7. Insider Threats & Privileged Account Misuse
- Identifies overprivileged user accounts and improper access control settings.
- Helps enforce role-based access control (RBAC) and regular access reviews.
- Prevents internal users from exploiting weak security policies.
8. Zero-Day Exploits
- Helps identify security flaws that could be targeted by attackers.
- Ensures continuous patching and threat monitoring.
- Provides proactive defense against emerging vulnerabilities.
9. IoT & Cloud Security Risks
- Identifies misconfigured cloud resources (AWS, Azure, Google Cloud).
- Prevents unauthorized access to IoT devices and industrial control systems.
- Helps implement cloud security posture management (CSPM).
10. Supply Chain Attacks
- Scans third-party integrations, software dependencies, and open-source vulnerabilities.
- Prevents attacks through compromised vendors, software libraries, or APIs.
- Ensures compliance with supply chain security standards.
Conducting a Vulnerability Assessment: The Complete Process
Step 1: Asset Inventory and Scope Definition
The first step is to identify and catalog all critical assets, including servers, databases, applications, endpoints, and network devices. Organizations often struggle with shadow IT, where employees use unauthorized software or devices that introduce security risks. To ensure a comprehensive assessment, businesses must map their entire attack surface, including cloud infrastructure, third-party services, and remote endpoints.
Step 2: Selecting the Right Vulnerability Scanning Tools
Vulnerability assessments can be conducted using automated tools, manual testing, or a combination of both. Automated tools like Nessus, Qualys, OpenVAS, Burp Suite, and Nikto scan systems for known vulnerabilities, while manual assessments help uncover business logic flaws and advanced security risks. Choosing the right scanner depends on factors like infrastructure size, compliance requirements, and security maturity.
Step 3: Conducting the Vulnerability Scan
Organizations must decide between authenticated and unauthenticated scans. Authenticated scans provide deeper insights into internal risks, while unauthenticated scans mimic external cyberattacks. Setting up a scanning schedule is crucial, some organizations conduct scans weekly, monthly, or after significant system changes to keep up with evolving threats.
Step 4: Analyzing and Prioritizing Vulnerabilities
Not all vulnerabilities pose an immediate risk. The Common Vulnerability Scoring System (CVSS) helps classify vulnerabilities based on their severity, exploitability, and potential impact. Risk-based prioritization ensures that organizations focus on fixing critical vulnerabilities first rather than attempting to patch every issue. AI-powered analysis tools assist security teams by triaging thousands of findings efficiently.
Step 5: Guided Remediation and Risk Mitigation
After identifying vulnerabilities, organizations must decide whether to apply patches, implement compensating controls, or accept the risk. Some vulnerabilities, such as those affecting legacy systems or third-party software, cannot be patched immediately. In such cases, alternative measures like web application firewalls (WAFs), network segmentation, and endpoint detection and response (EDR) solutions help reduce the risk.
Step 6: Reporting and Continuous Monitoring
A well-structured vulnerability assessment report should include findings, risk scores, remediation recommendations, and timelines. Security teams should track key metrics like Time to Remediate (TTR) and vulnerability recurrence rates to measure security improvements. Continuous monitoring, rather than one-time assessments, is essential for maintaining a strong security posture in a constantly changing threat environment.
Also Read: Continuous Threat Exposure Management (CTEM) – The Ultimate Guide for CISOs
How to Communicate Vulnerabilities as Business Risks?
Vulnerabilities should not be viewed as isolated technical issues but rather as business risks that can affect operations, financial stability, regulatory compliance, and reputation. Security teams must translate technical findings into business impact for executives and decision-makers.
- Quantify Impact: Express risks in terms of potential financial loss, operational downtime, and data breach costs. Use industry benchmarks and historical incident costs to provide context.
- Use Risk Scoring Models: Assign risk ratings to vulnerabilities based on exploitability, business criticality, and potential impact. The CVSS (Common Vulnerability Scoring System) and risk-based prioritization models help focus efforts on high-impact threats.
- Align with Business Objectives: Show how vulnerabilities can disrupt critical business functions, customer trust, and compliance mandates.
- Leverage Executive Dashboards: Provide clear, non-technical reports that highlight key risks, remediation timelines, and resource needs.
By aligning vulnerabilities with business risks, organizations can prioritize remediation efforts effectively and ensure security investments are directed toward high-risk areas.
Mapping Vulnerabilities to Regulatory Compliance Frameworks
Organizations must ensure that vulnerability assessments align with industry regulations and cybersecurity frameworks to maintain compliance and avoid penalties. Mapping vulnerabilities to compliance frameworks helps demonstrate due diligence and security maturity.
PCI-DSS (Payment Card Industry Data Security Standard)
- Requires regular vulnerability scans and penetration testing for systems handling payment data.
- Demands timely patching of high-risk vulnerabilities and proper network segmentation.
- Organizations must ensure that vulnerability management processes meet PCI DSS Requirement 11 for continuous security monitoring.
ISO 27001 (International Standard for Information Security Management)
- Focuses on risk-based vulnerability management as part of an ISMS (Information Security Management System).
- Requires organizations to identify, assess, and mitigate vulnerabilities to protect the confidentiality, integrity, and availability of information.
- Vulnerability assessments contribute to Annex A.12.6.1 (Management of technical vulnerabilities) by ensuring timely remediation.
NIST (National Institute of Standards and Technology)
- NIST SP 800-53 and SP 800-171 outline security controls for federal agencies and contractors.
- Emphasizes continuous vulnerability monitoring and risk-based mitigation strategies.
- Aligns with the NIST Cybersecurity Framework (CSF), which categorizes vulnerabilities under the “Protect” and “Detect” functions.
Industry-Specific Vulnerability Assessments
Different industries have unique security challenges and regulatory requirements, making it essential to tailor vulnerability assessments based on sector-specific risks. Here’s how vulnerability assessments apply to key industries:
1. Healthcare: Protecting Patient Data and Complying with HIPAA
The healthcare sector is a prime target for cyberattacks due to the sensitive nature of electronic health records (EHRs), patient data, and medical devices. A vulnerability assessment in healthcare focuses on:
- HIPAA Compliance: Identifying security gaps in compliance with HIPAA Security Rule, which mandates the protection of protected health information (PHI).
- Medical Device Security: Ensuring IoT-connected medical devices (MRI machines, infusion pumps, pacemakers) are free from vulnerabilities that could be exploited.
- Network Segmentation: Assessing hospital networks to prevent attacks from spreading across patient databases, administration systems, and medical devices.
- Ransomware Prevention: Detecting vulnerabilities that could lead to ransomware attacks, which have become a major threat in healthcare.
2. Finance: Securing Financial Transactions and Meeting PCI-DSS Requirements
The financial industry manages high-value transactions, customer banking data, and payment systems, making it a frequent target for fraud and cybercrime. A vulnerability assessment in finance focuses on:
- PCI-DSS Compliance: Ensuring systems handling credit card transactions meet Payment Card Industry Data Security Standard (PCI-DSS) requirements, including regular vulnerability scanning and penetration testing.
- Fraud Prevention: Detecting vulnerabilities in online banking portals, ATMs, and mobile payment applications to prevent unauthorized access.
- API Security: Securing financial APIs used in digital banking, fintech applications, and payment processing systems.
- DDoS Resilience: Assessing financial networks for weaknesses that could be exploited in distributed denial-of-service (DDoS) attacks.
3. Retail: Safeguarding Customer Data and E-Commerce Platforms
Retailers handle large volumes of customer data, payment transactions, and supply chain logistics, making them a target for cyber criminals. A vulnerability assessment in retail focuses on:
- E-Commerce Security: Scanning online platforms for vulnerabilities like SQL injection (SQLi), cross-site scripting (XSS), and insecure payment gateways.
- Customer Data Protection: Identifying risks related to storing and processing customer information, including payment details and personal data.
- Point-of-Sale (POS) Security: Detecting vulnerabilities in POS systems, which are often targeted in credit card skimming and malware attacks.
- Third-Party Risk Management: Assessing vulnerabilities introduced by third-party vendors, supply chain partners, and cloud-based retail platforms.
4. Small Businesses: Affordable and Scalable Solutions for SMBs
Small and medium-sized businesses (SMBs) often lack large security teams and budgets, making them high-risk targets for cyberattacks. A vulnerability assessment for SMBs focuses on:
- Cost-Effective Security Solutions: Using affordable vulnerability scanners (OpenVAS, Nessus Essentials, Qualys Community Edition) to identify security risks.
- Cloud Security: Protecting cloud-based applications, SaaS tools, and remote work environments from unauthorized access.
- Employee Awareness: Identifying vulnerabilities caused by weak passwords, phishing attacks, and social engineering threats.
- Basic Compliance Readiness: Ensuring SMBs meet essential security guidelines like GDPR, ISO 27001, or SOC 2 without excessive costs.
Also Read: Cybersecurity Budgets Set to Grow by 9%: What It Means for Companies?
Common Mistakes in Vulnerability Assessments
Vulnerability assessments are essential for identifying security weaknesses, but many organizations make critical mistakes that reduce their effectiveness. Here’s a breakdown of the most common errors:
1. Skipping Asset Discovery
One of the biggest mistakes is not having a complete inventory of IT assets before starting the assessment. Organizations often overlook:
- Shadow IT: Unauthorized devices, applications, and cloud services that employees use without IT approval.
- Legacy Systems: Older infrastructure that may not be actively monitored but still presents security risks.
- Cloud and Third-Party Assets: External systems connected to the organization that could introduce vulnerabilities.
Without a comprehensive asset inventory, the vulnerability assessment will be incomplete, leaving security gaps that attackers can exploit.
2. Relying Solely on Automated Tools
Automated scanners like Nessus, OpenVAS, and Qualys are valuable, but they cannot identify all security risks. Organizations that solely depend on automated tools may miss:
- Business Logic Flaws: Issues related to how an application processes transactions or permissions, which automated tools cannot detect.
- Zero-Day Vulnerabilities: Newly discovered threats that are not yet in vulnerability databases.
- False Positives: Automated scans sometimes flag non-existent issues, wasting time on unnecessary remediation.
A hybrid approach that combines automated scanning with manual testing (such as penetration testing) provides a more accurate assessment.
3. Ignoring Low-Risk Vulnerabilities
Organizations often focus only on high and critical vulnerabilities, ignoring low-risk findings. However, low-severity issues can still be exploited in combination with other vulnerabilities, leading to major security incidents. Examples include:
- Information Disclosure: Seemingly harmless data exposure (e.g., error messages, email addresses) can provide attackers with useful reconnaissance information.
- Unpatched Low-Risk Bugs: Attackers may chain together multiple low-severity vulnerabilities to escalate privileges or gain deeper access.
- Default Credentials: A minor misconfiguration can turn into a major risk if default admin credentials are left unchanged.
A risk-based approach should consider exploitability, attack chains, and potential business impact, not just severity scores.
4. Failing to Retest After Remediation
Many organizations fix vulnerabilities but do not verify if the remediation was successful. This can lead to:
- Patch Failures: Updates may not apply correctly or introduce new issues.
- Workarounds Instead of Fixes: Temporary mitigations (e.g., firewall rules) may reduce risk temporarily but not eliminate the root cause.
- Reintroduced Vulnerabilities: Some security fixes get overwritten in future updates or configuration changes.
A proper vulnerability management program includes post-remediation testing to confirm that fixes are effective and do not introduce new weaknesses.
5. Not Aligning Assessments with Compliance Requirements
Vulnerability assessments should map findings to regulatory frameworks like PCI-DSS, HIPAA, NIST, ISO 27001, and GDPR. Common compliance mistakes include:
- Infrequent Scans: Some regulations (e.g., PCI-DSS) require quarterly vulnerability scans and continuous monitoring.
- Lack of Documentation: Failing to document findings, remediation efforts, and security improvements can lead to compliance violations.
- Focusing Only on Compliance: Some organizations prioritize passing audits rather than truly improving security. Compliance should be a byproduct of strong security practices, not just a checkbox.
Vulnerability Assessment Best Practices for Effective Security Testing
Conduct Regular Assessments
Cyber threats evolve continuously, and vulnerabilities emerge due to new exploits, system updates, and configuration changes. Regular assessments help organizations:
- Identify and remediate vulnerabilities before attackers can exploit them.
- Stay compliant with industry regulations like PCI-DSS, HIPAA, and ISO 27001, which mandate periodic security checks.
- Reduce the risk of zero-day exploits by ensuring that security scans are frequent and updated.
Organizations should schedule monthly, quarterly, or real-time continuous assessments based on their risk profile and industry standards.
Combine Automated Tools with Manual Testing
While automated scanners like Nessus, Qualys, and OpenVAS are great for identifying known vulnerabilities, they cannot detect:
- Business logic flaws that attackers could exploit for privilege escalation.
- Chained attack scenarios that combine multiple low-risk vulnerabilities into a serious breach.
- Zero-day vulnerabilities that require advanced penetration testing techniques.
A hybrid approach, combining automated scanning with manual testing (ethical hacking, red teaming, penetration testing), ensures a more comprehensive security evaluation. Platforms like Strobes bridge this gap by offering a unified security approach, integrating automated scanning with human-driven penetration testing
Prioritize Vulnerabilities Based on Risk
Not all vulnerabilities require immediate remediation. Organizations should prioritize based on real-world risk factors, rather than solely relying on CVSS scores. Effective prioritization considers:
- Exploitability: Is the vulnerability actively exploited in the wild?
- Business Impact: Could the issue affect critical systems, financial transactions, or sensitive data?
- Attack Surface Exposure: Is the vulnerability externally facing, or is it limited to internal users?
Using risk-based vulnerability management (RBVM) tools and AI-powered analysis can help focus remediation efforts on the most critical threats first.
Train Employees on Cybersecurity Awareness
Human error remains a leading cause of security breaches. Even the most advanced vulnerability assessments are ineffective if employees:
- Fall for phishing attacks and expose credentials.
- Use weak passwords or reuse them across multiple accounts.
- Accidentally misconfigure cloud services, exposing sensitive data.
Regular cybersecurity training should include phishing simulations, secure coding practices, and incident response exercises to reduce human-driven security risks.
Integrate Vulnerability Assessments into DevSecOps
Traditional security assessments often slow down development, creating friction between security and DevOps teams. Integrating vulnerability assessments into DevSecOps ensures that security is built into the software development lifecycle (SDLC). Key approaches include:
- Automated security scanning within CI/CD pipelines to catch vulnerabilities before deployment.
- Shift-left security by conducting vulnerability scans during code development and testing stages.
- Secure coding practices to reduce common flaws like SQL injection, XSS, and insecure authentication.
Challenges in Vulnerability Assessment
1. Incomplete Asset Discovery
One of the biggest challenges in vulnerability assessments is failing to identify all assets within an organization’s IT environment. Organizations often struggle with:
- Shadow IT: Employees use unauthorized applications and cloud services, creating unmonitored security risks.
- Legacy Systems: Older infrastructure is often forgotten or unpatched, leaving it vulnerable to attacks.
- Third-Party Integrations: External vendors and partners introduce risks that organizations fail to assess properly.
2. High Volume of Vulnerabilities
Modern enterprises generate thousands of security findings from automated scans, making it difficult to prioritize remediation. Many organizations struggle with:
- Duplicate and redundant findings from multiple security tools.
- Alert fatigue, where security teams are overwhelmed by the volume of issues.
- Lack of risk-based prioritization, leading to time wasted on low-impact vulnerabilities.
A risk-based approach, like Strobes CTEM, helps reduce noise by consolidating vulnerabilities and prioritizing them based on exploitability, business impact, and active threats.
3. Relying Solely on Automated Scanning
Automated vulnerability scanners like Nessus, Qualys, and OpenVAS are essential but cannot detect all risks. These tools miss:
- Business logic flaws (e.g., bypassing authentication mechanisms).
- Zero-day vulnerabilities that are not yet in security databases.
- Complex attack chains where multiple low-risk vulnerabilities combine into a critical threat.
Combining automated scanning with manual penetration testing ensures a more complete assessment of security risks.
4. False Positives and False Negatives
Automated scanners can generate false positives, flagging harmless issues as vulnerabilities, which wastes security teams’ time. On the other hand, false negatives occur when real vulnerabilities are overlooked, giving organizations a false sense of security.
- False positives increase remediation efforts for issues that do not pose actual risks.
- False negatives leave organizations exposed to hidden threats that remain undetected.
Using AI-powered triage tools like Strobes’ risk-based prioritization engine helps filter out false positives and focus remediation on actual threats.
5. Lack of Skilled Security Professionals
There is a shortage of cybersecurity experts who can analyze vulnerabilities, perform manual testing, and guide remediation efforts. Many organizations struggle with:
- Limited in-house security teams that cannot keep up with assessments.
- Dependence on third-party consultants, which adds cost and time delays.
- Lack of expertise in advanced attack scenarios, such as API security flaws, cloud misconfigurations, and emerging threats.
Leveraging Pentesting-as-a-Service (PTaaS) solutions, like those offered by Strobes, provides on-demand security expertise without requiring large in-house teams.
6. Delays in Guided Remediation
Identifying vulnerabilities is only half the battle—remediation requires cross-team coordination, patching efforts, and security validations. Common remediation challenges include:
- Patching delays due to legacy systems, vendor dependencies, or downtime concerns.
- Lack of communication between security, IT, and DevOps teams.
- Limited automation, leading to manual effort in applying security fixes.
Using integrated security workflows and automated ticketing systems (e.g., Jira, ServiceNow integrations) streamlines remediation processes and reduces risk exposure.
7. Compliance and Regulatory Challenges
Organizations in regulated industries (finance, healthcare, retail) must align vulnerability assessments with compliance standards such as:
- PCI-DSS (for payment security).
- HIPAA (for healthcare data protection).
- ISO 27001 and NIST (for general cybersecurity best practices).
Failure to conduct assessments on time, document findings, and remediate vulnerabilities can result in regulatory fines and reputational damage.
8. Lack of Continuous Monitoring
Many organizations treat vulnerability assessments as a one-time process, scanning systems only once a year for compliance. However, threats evolve daily, making continuous vulnerability management essential.
- New vulnerabilities emerge regularly in software, cloud services, and applications.
- Attackers constantly develop new exploitation techniques.
- Unpatched vulnerabilities remain a major entry point for cyberattacks.
Shifting to Continuous Threat Exposure Management (CTEM), as provided by Strobes, ensures real-time vulnerability monitoring, proactive risk mitigation, and continuous security posture improvement.
Conclusion
A one-time vulnerability scan isn’t enough when new threats emerge daily. Organizations need a risk-driven, continuous approach that goes beyond basic scanning.
By combining automation with expert analysis, prioritizing vulnerabilities based on real-world impact, and embedding security into DevSecOps, teams can stop chasing false alarms and focus on real threats.
With platforms like Strobes CTEM, it’s not just about finding vulnerabilities, it’s about fixing them faster and smarter. A strong vulnerability assessment program isn’t just a compliance checkbox, it’s a way to reduce risk, stay prepared, and keep your business running smoothly. The choice is simple: act now or react later.
Related Reads:
- Top 15 Vulnerability Management Tools for Your Business
- Vulnerability Management Lifecycle: The Ultimate Guide to Business Security
- What is Vulnerability Management? Compliance, Challenges, & Solutions
- Top 5 Vulnerability Management Mistakes Companies Make (Plus a Bonus Mistake to Avoid)
- eBook: The Vulnerability Management Buyer’s Guide
- Solution: Risk Based Vulnerability Management
 1. Network-Based Vulnerability Assessment
1. Network-Based Vulnerability Assessment