Cyberattacks are growing more sophisticated by the day, especially with the advent of AI. Hackers are exploiting not just software flaws, but also misconfigurations, human error, and even unguarded cloud assets. Making the shift from Vulnerability Management To CTEM is crucial — traditional vulnerability management, focused solely on patching known weaknesses, is like playing whack-a-mole in a volcanic eruption.
It's time for a new approach: Continuous Threat Exposure Management (CTEM). This proactive strategy goes beyond patching to provide a complete picture of your organisation's security posture, helping you anticipate and prevent attacks before they happen.
For years, vulnerability management (VM) has been the workhorse of cybersecurity, diligently identifying, prioritizing, and fixing weaknesses in systems and software. It's a three-pronged approach:
While these practices offer valuable defensive measures, VM programs often face limitations:
These limitations can leave organizations vulnerable to sophisticated modern attacks that exploit previously unknown vulnerabilities, misconfigurations, or human error.
Cybersecurity is a constant battle against evolving threats. Traditional vulnerability management (VM) programs have been like plugging holes in a sinking ship – they address immediate problems, but the underlying weaknesses remain. To truly stay afloat, organizations need a more comprehensive solution, continuous threat exposure management (CTEM).
Here's why Continuous Threat Exposure Management(CTEM) is a game-changer:
Also Read: How CTEM Enhances Threat Prioritization in Complex Networks
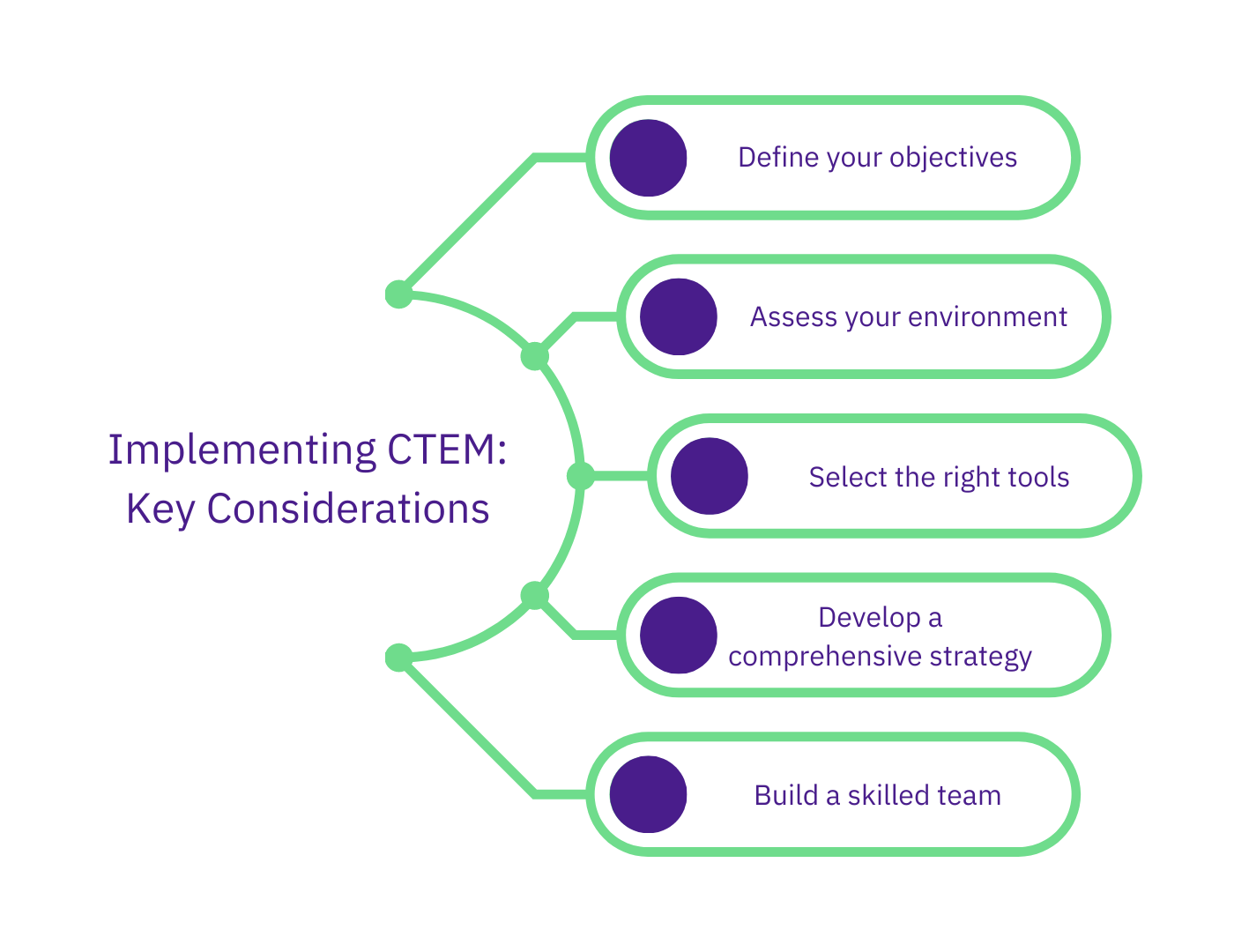
While the transition from Vulnerability Management To CTEM offers significant benefits, it's crucial to consider key factors for successful implementation:
By proactively and strategically making the shift from Vulnerability Management To CTEM, organizations gain a significant advantage in the ever-changing cyber threat environment. They can move beyond simply identifying and patching vulnerabilities to actively managing their overall threat exposure and building a more robust security posture. Request a demo today to see how CTEM can strengthen your security strategy.
When shifting from Vulnerability Management (VM) to CTEM, useful metrics include Mean Time to Remediate (MTTR), exploit frequency on threats, percentage of misconfigurations, and exposure of externally facing assets. These metrics enable leaders to quantify risk reduction and align security efforts with frameworks such as NIST or ISO 27001.
No. Vulnerability scanning remains foundational in discovering known weaknesses, but CTEM complements scanning by adding context, threat intelligence, and ongoing validation. Together, they provide decision-makers with both breadth and actionable insight.
CTEM reduces waste spent on low-impact vulnerabilities by focusing remediation on issues that pose real risk. This leads to more efficient use of budget and personnel. Enterprises often observe a 30-50% reduction in effort for high-severity remediation cycles after adopting CTEM.
CTEM helps organizations map their threat exposure to regulatory controls in SOC 2, PCI DSS, and ISO 27001. Because reporting includes validated findings and risk scores, audit preparation becomes faster and more reliable.
CTEM integrates threat intelligence feeds to detect emerging or zero-day threats. While scan-based tools identify known vulnerabilities, CTEM highlights unknown risk by monitoring indicators of exploitation and external threat movements to prioritize defense.