
We must be able to stop, identify, respond to, and recover from cyberattacks to reduce the risk of a security incident and avoid the expense of one. By ensuring that all known software vulnerabilities are fixed and by conducting routine security assessments to find any potential undiscovered flaws, we can stop many assaults. However, we can never ensure that a system will always be secure.
A proper process for detecting, responding to, and recovering from incidents is required. Here, we'll be concentrating on why it's important to conduct a security assessment, such as penetration testing on our IT infrastructure, to stop these unpleasant situations from occurring.Penetration testing, sometimes referred to as ethical hacking, white-hat hacking, or pen-testing, is a type of security evaluation that evaluates a computer system, network, or software application to uncover security weaknesses that an attacker could exploit. Depending on our requirements, the penetration tests scope may change.
Known as Red-Teaming or Adversarial Simulation, it can range from a straightforward penetration test on a single online application to a comprehensive test on the entire business.Through the identification of exploitable flaws in security defenses, pen-testing, also known as penetration testing, seeks to enhance security. To evaluate the security posture of an application or network, it offers a thorough study of several simulated assaults.
Penetration testing is a great approach to uncover holes at a specific moment and have long been a crucial component of many organizations’ strategies to defend themselves from cyberattack.
The most difficult and demanding of all the cyber issues is penetration testing. Penetration testing involves assaulting a company's systems and infrastructure to check for security and vulnerability. A great technique to confirm the security of your website is through penetration testing.It's critical to understand your weaknesses and the potential attack vectors for them. Make a list of every asset you must establish a clear plan and scope for exposure detection. Teams that agree about the specifics, the scope, and the preparation provide tests that are more thorough and produce better results. To verify that remedies are successful, it is crucial to test and retest vulnerabilities over time. The best time to perform a pen test is just before an assault when assets are most exposed.
By avoiding and minimising intrusions into the IT infrastructure, regular penetration testing helps avoid these costs.
Now that everyone is aware of the benefits of pentesting, let's learn about the best tips for an efficient pentesting program.

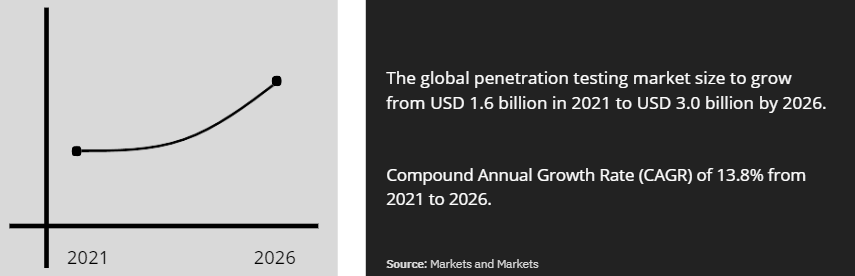
So as a means of ensuring additional security, penetration testing services are becoming increasingly important and are predicted to grow quickly alongside the cloud computing industry.
Strobes PTaaS combines the human element of pen testing with the efficiency of a SaaS delivery platform to enable real-time collaboration and quicker cleanup. Understanding the importance of penetration testing, we offer a broad range of penetration testing services to help organizations strengthen their security posture. Our list of penetration tests is available to address diverse security needs. Every organization has a different technology architecture, and we integrate with the corresponding security priorities to ensure comprehensive protection. Our pen-testing insights, from testing to mitigation, are delivered right into your DevOps pipeline using Jira, GitHub, or the Strobes API. Anytime you need them, our pen testing staff is always available. Throughout the process, you have access to pen-testers and real-time insight to assist you in quickly prioritizing and mitigating vulnerabilities. With the expertise of dealing with over 150+ customers globally, we now have our resources on the ground to provide managed products and services to our end customers. Ready to strengthen your security posture? Schedule a demo with Strobes and take the first step toward a more secure future.Related Reads: