
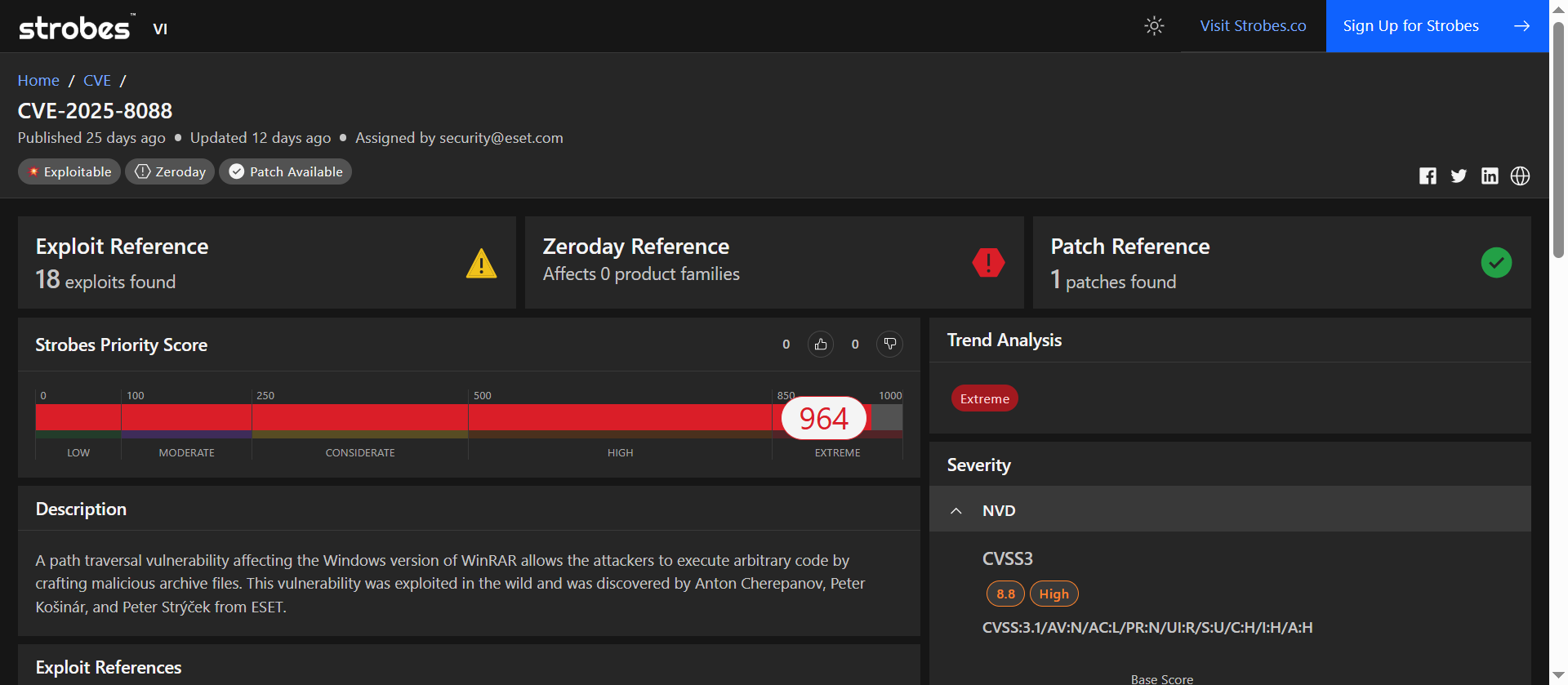
| Field | Details |
| CVSS v3.1 | 8.8 (High) |
| Strobes Priority Score | 964 / 1000 (Critical) |
| Exploit Availability | Actively exploited in the wild |
| Patch Available | Yes (WinRAR 7.13) |
| Vulnerability Type | Directory Traversal |
| Affected Versions | WinRAR versions prior to 7.13 |
| CISA KEV Catalog | Yes (Action due by 2025-09-02) |
| Mitigation Step | Status |
| Patch Availability | WinRAR 7.13 released on 2025-07-30 |
| Exploit Activity | Actively exploited in the wild |
| Immediate Workaround | Upgrade to WinRAR 7.13 |
| Hardening Tip | Use Windows Software Restriction Policies (SRP) and Image File Execution Options (IFEO) to block unauthorized executables |
| Detection | Monitor for unusual file extraction activities and the presence of unauthorized executables in startup directories |
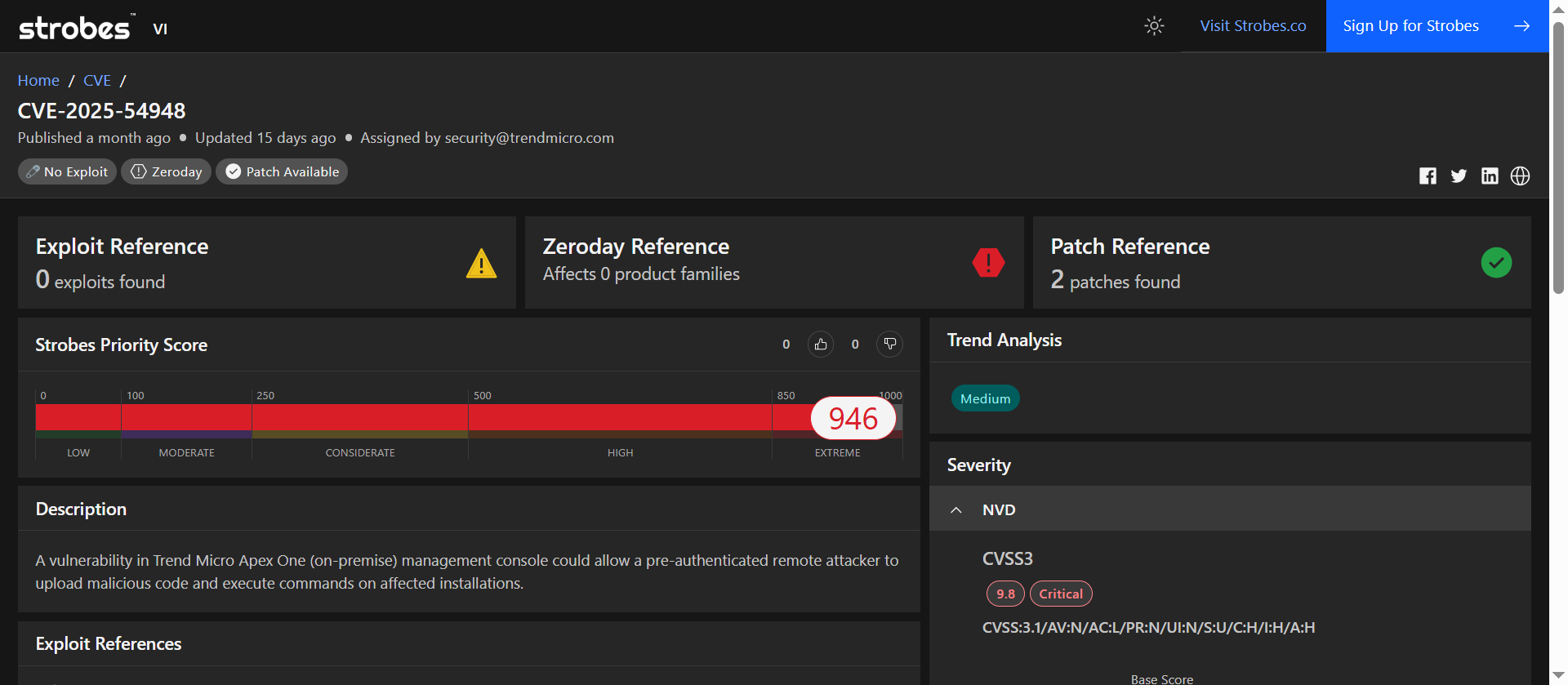
| Field | Details |
| CVSS v3.1 | 9.4 (Critical) |
| Strobes Priority Score | 946 / 1000 (Critical) |
| Exploit Availability | Actively exploited in the wild |
| Patch Available | Yes (FixTool_Aug2025 and Critical Patch) |
| Vulnerability Type | OS Command Injection |
| Affected Versions | Apex One 2019 Management Server Version 14039 and below |
| CISA KEV Catalog | Yes (Action due by 2025-09-08) |
| Mitigation Step | Status |
| Patch Availability | FixTool_Aug2025 (Short-term Mitigation) and Critical Patch released on August 15, 2025 |
| Exploit Activity | Actively exploited in the wild |
| Immediate Workaround | Apply FixTool_Aug2025 to block known exploits |
| Hardening Tip | Restrict access to the Management Console by implementing source IP restrictions |
| Detection | Monitor for unusual file uploads and command executions on the Management Console |
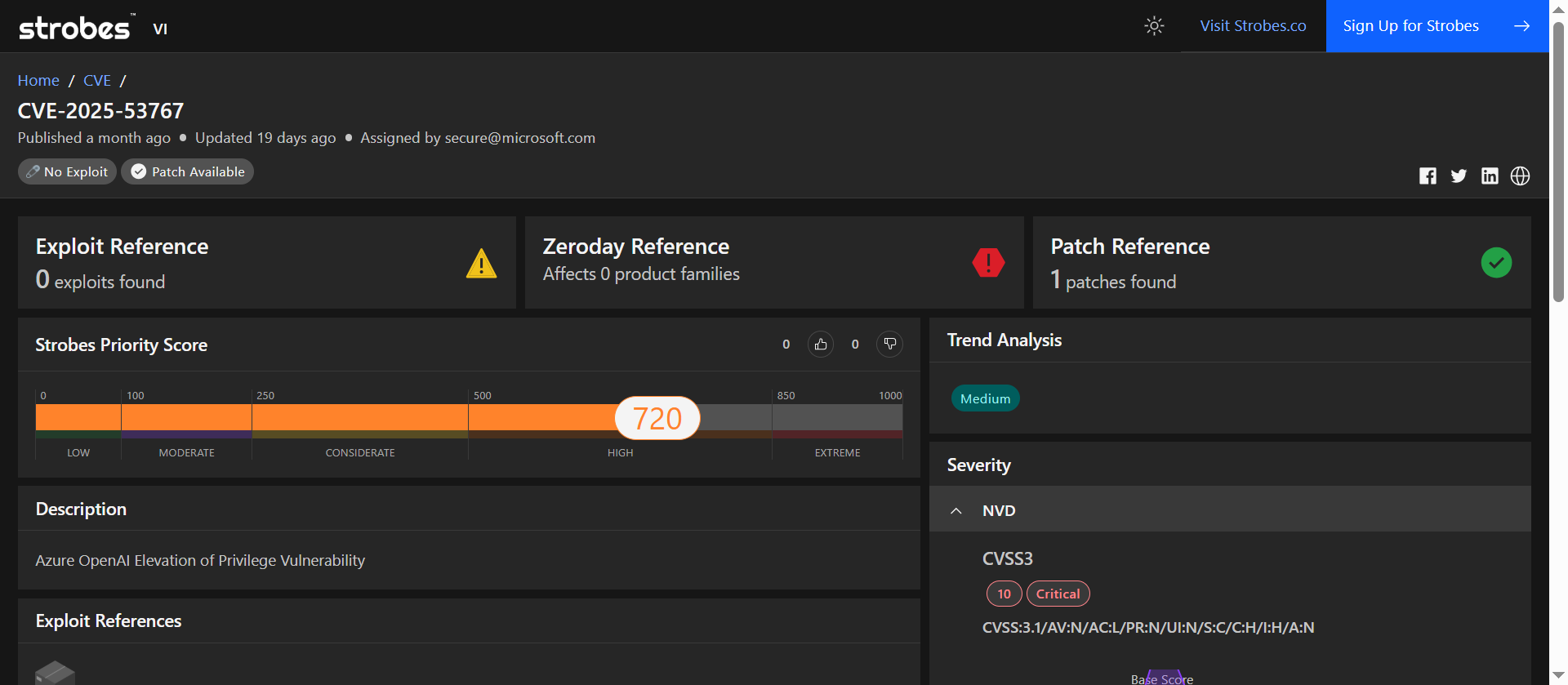
| Field | Details |
| CVSS v3.1 | 10.0 (Critical) |
| Strobes Priority Score | 720 / 1000 (High) |
| Exploit Availability | No public exploit reported |
| Patch Available | Yes (Released August 2025) |
| Vulnerability Type | Server-Side Request Forgery (SSRF) |
| Affected Versions | All Azure OpenAI services prior to the patch |
| Mitigation Step | Status |
| Patch Availability | Microsoft released patches in August 2025 |
| Exploit Activity | No public exploit reported |
| Immediate Workaround | Apply the latest security updates from Microsoft |
| Hardening Tip | Review and restrict network access controls to internal endpoints |
| Detection | Monitor for unusual request patterns or unauthorized access attempts |
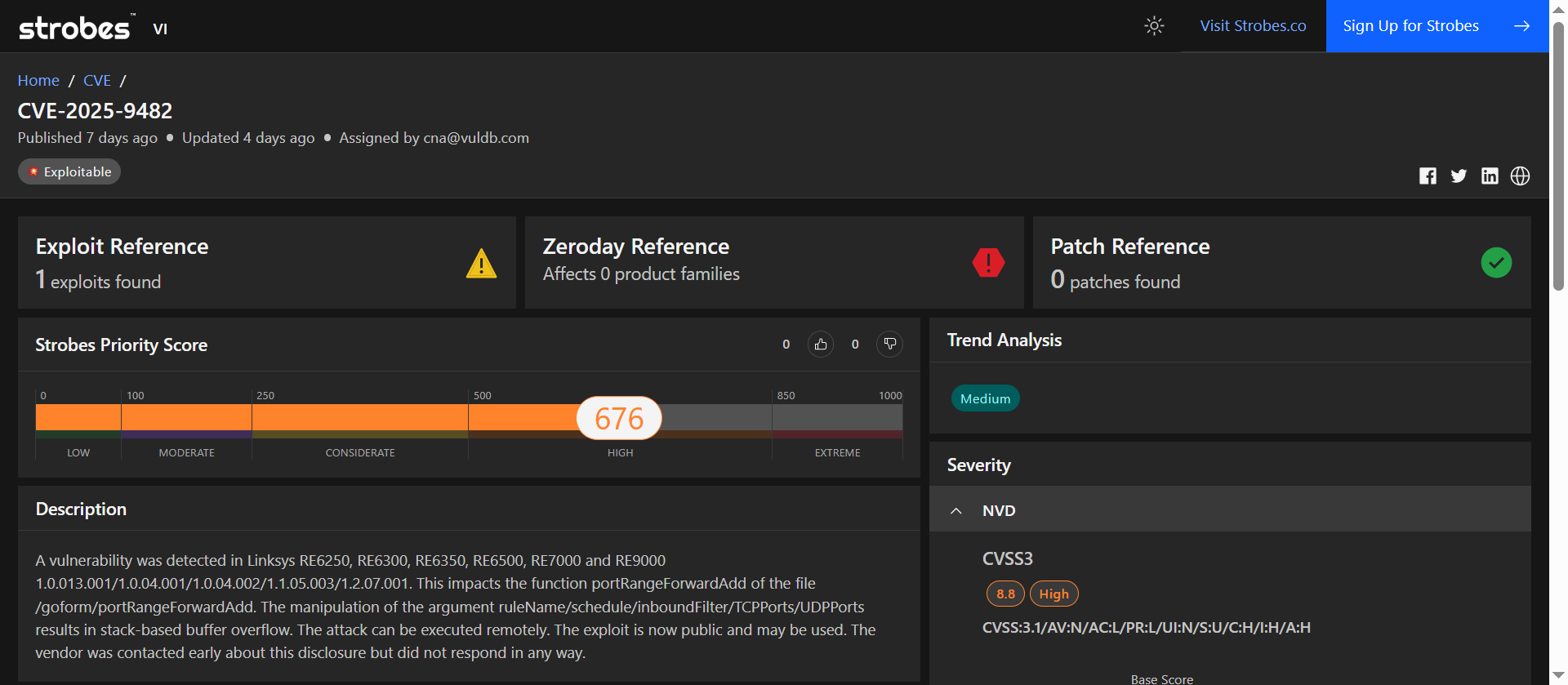
| Field | Details |
| CVSS v3.1 | 8.8 (High) |
| Strobes Priority Score | 676 / 1000 (High) |
| Exploit Availability | 1 known public exploit |
| Patch Available | No patch available |
| Trend Analysis | High (actively exploited, ongoing attacks) |
| Vulnerability Type | Stack-based buffer overflow |
| Affected Versions | RE6250, RE6300, RE6350, RE6500, RE7000, RE9000 |
| Mitigation Step | Status |
| Patch Availability | No patch released as of September 2025 |
| Exploit Activity | Public exploit available, actively exploited |
| Immediate Workaround | Isolate vulnerable devices from critical network segments |
| Hardening Tip | Use firewalls to block access to vulnerable ports and endpoints |
| Detection | Monitor for unusual requests to /goform/portRangeForwardAdd endpoint |
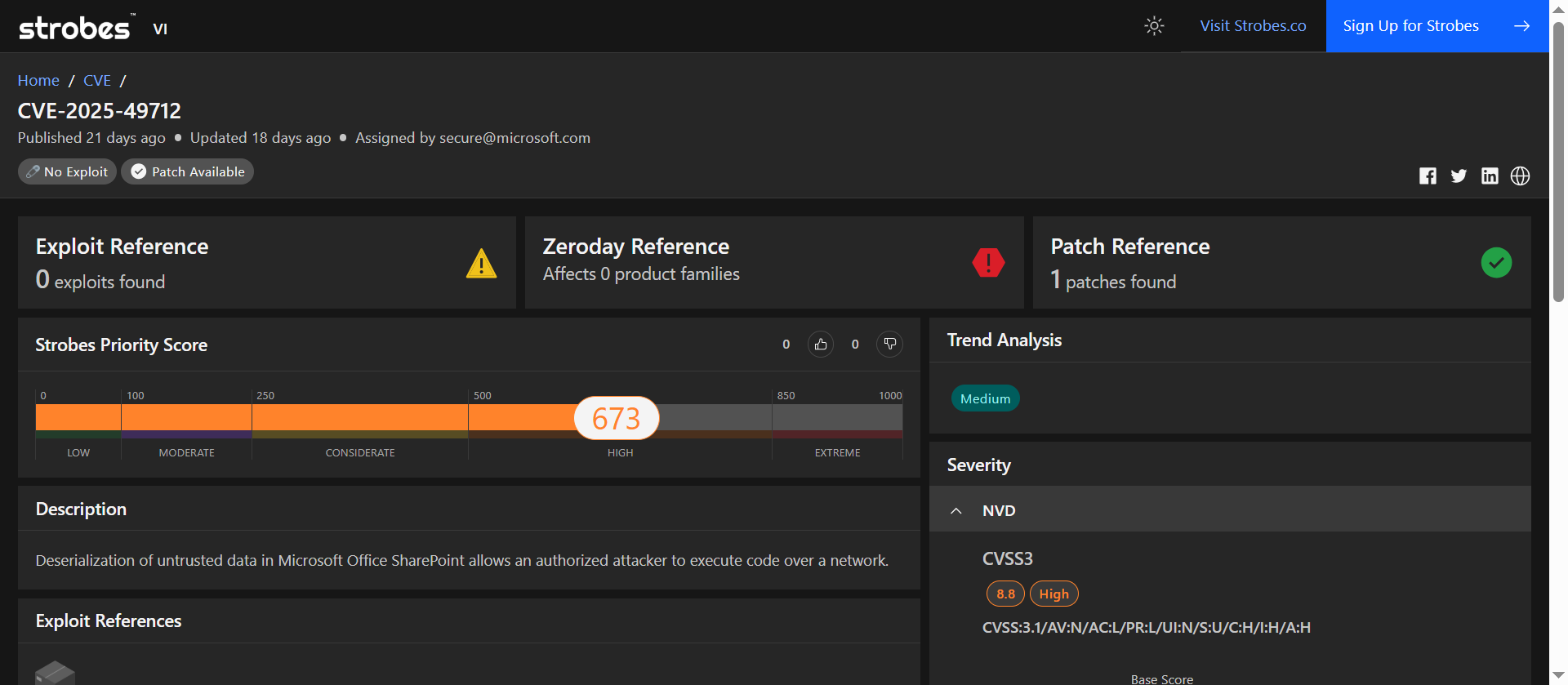
| Field | Details |
| CVSS v3.1 | 8.8 (High) |
| Strobes Priority Score | 673 / 1000 (High) |
| Exploit Availability | No public exploit reported |
| Patch Available | Yes (August 2025 Patch Tuesday) |
| Vulnerability Type | Deserialization of untrusted data |
| Affected Versions | SharePoint Server 2016, 2019 |
| Mitigation Step | Status |
| Patch Availability | Security updates released on August 12, 2025 |
| Exploit Activity | No public exploit reported |
| Immediate Workaround | Apply the security updates promptly |
| Hardening Tip | Restrict Site Owner privileges to trusted users |
| Detection | Monitor for unusual activities in SharePoint logs |
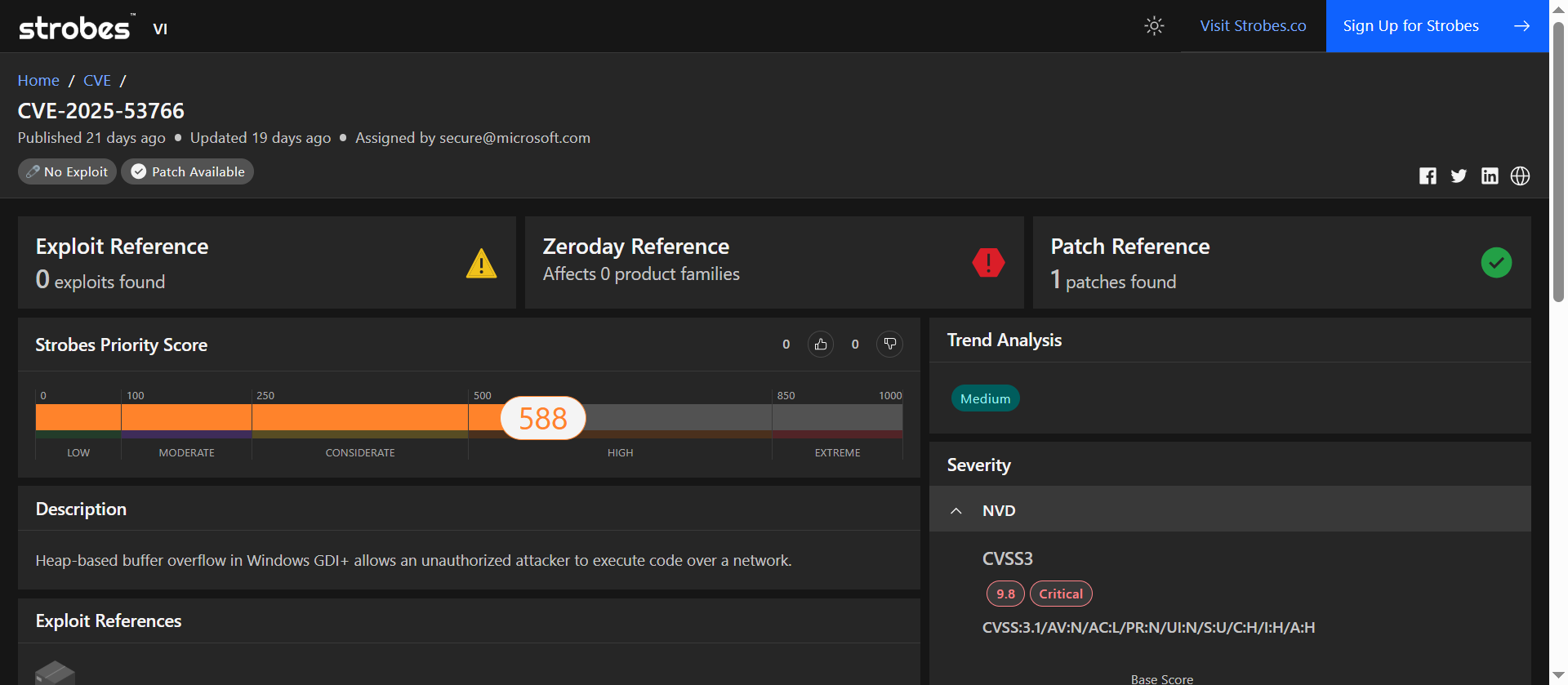
| Field | Details |
| CVSS v3.1 | 9.8 (Critical) |
| Strobes Priority Score | 588 / 1000 (High) |
| Exploit Availability | No known public exploits |
| Patch Available | Yes (August 2025 Patch Tuesday) |
| Vulnerability Type | Heap-based buffer overflow |
| Affected Versions | Windows Server 2008 SP2, 2016, 2019, 2022, 2025; Windows 10 versions 1507–22H2; Windows 11 versions 22H2–24H2; Microsoft Office for Universal and Android versions prior to 16.0.14326.22618 and 16.0.19127.20000, respectively. |
| Mitigation Step | Status |
| Patch Availability | Microsoft released a patch on August 12, 2025. |
| Exploit Activity | No known public exploits; however, the high CVSS score and active exploitation potential warrant immediate attention. |
| Immediate Workaround | Apply the security update provided by Microsoft. |
| Hardening Tip | Ensure that all systems are updated with the latest security patches and consider implementing application whitelisting to prevent unauthorized code execution. |
| Detection | Monitor for unusual document processing activities and unauthorized access attempts to sensitive systems. |