As September comes to a close, we’ve seen some fresh vulnerabilities emerge that demand immediate attention. From critical flaws in widely used software to newly discovered loopholes that could impact security across industries, these CVEs have been making waves. Whether you’re securing networks or locking down sensitive systems, staying on top of these threats is crucial. Let’s break down the top five CVEs of September and why they need to be on your radar right now!
CVE-2024-43491 is a critical remote code execution vulnerability in Microsoft Windows Update, specifically affecting the Servicing Stack of Windows 10 Version 1507. This vulnerability allows attackers to exploit previously mitigated vulnerabilities due to a rollback of fixes in a March 2024 update.
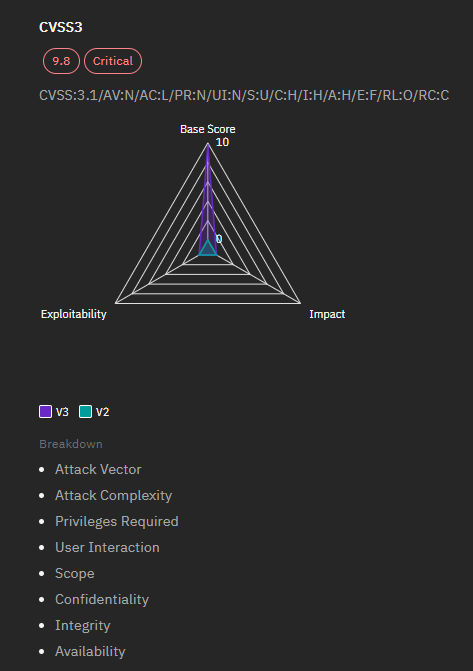
By exploiting this vulnerability, an attacker can manipulate the application to process a malicious PHP file instead of the intended one. This could lead to various malicious activities, including data theft, system compromise, or denial of service.
The vulnerability allows an attacker to exploit systems running the affected versions of Windows 10 by leveraging rolled-back fixes from previous updates. Successful exploitation could lead to remote code execution, thereby allowing attackers to execute arbitrary code on the target system without user interaction.
To mitigate this vulnerability, it is essential to:
This CVE has been added to CISA's Known Exploited Vulnerabilities Catalog, indicating its significance and the urgency for remediation. It is critical for organizations using affected versions of Windows to apply patches promptly to avoid potential exploitation.
Timeline
CVE-2024-38194 is a Critical Remote Code Execution (RCE) vulnerability affecting Azure Web Apps, allowing authenticated attackers to exploit an authorization flaw.
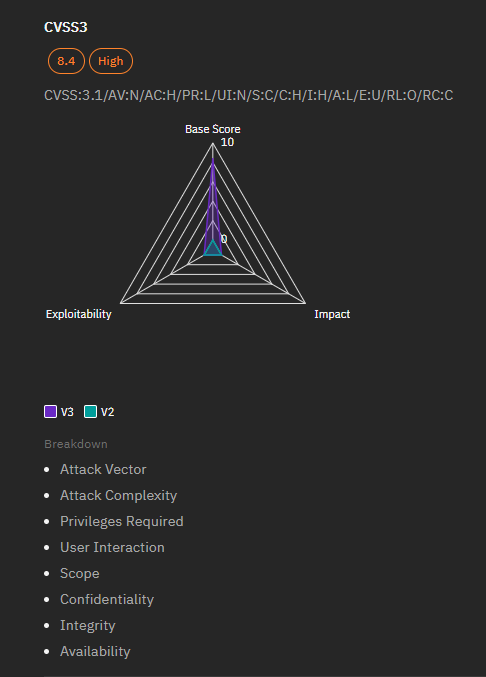
An authenticated attacker can leverage the improper authorization vulnerability to elevate their privileges within the Azure Web Apps environment, potentially compromising sensitive data and operations.
Microsoft has fully addressed this vulnerability within the Azure infrastructure, and users of the affected service do not need to take further action. The publication of this CVE is intended for transparency regarding the issue and its resolution.
This vulnerability underscores the importance of robust authorization mechanisms in cloud services to prevent privilege escalation attacks.
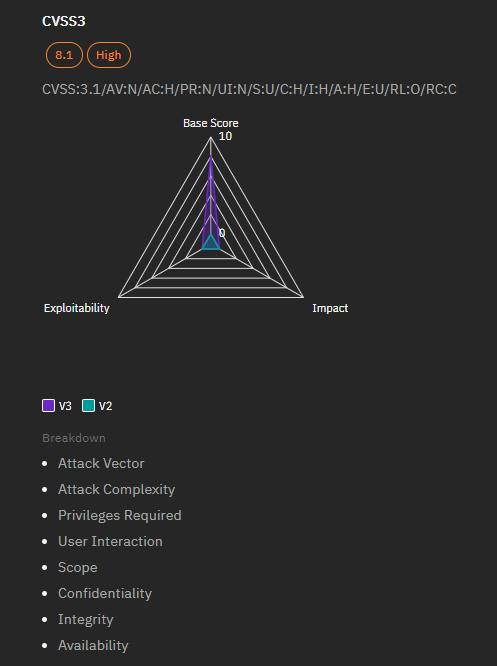
CVE-2024-37341 is a Microsoft SQL Server Elevation of Privilege Vulnerability that allows unauthorized users to gain elevated access to resources.
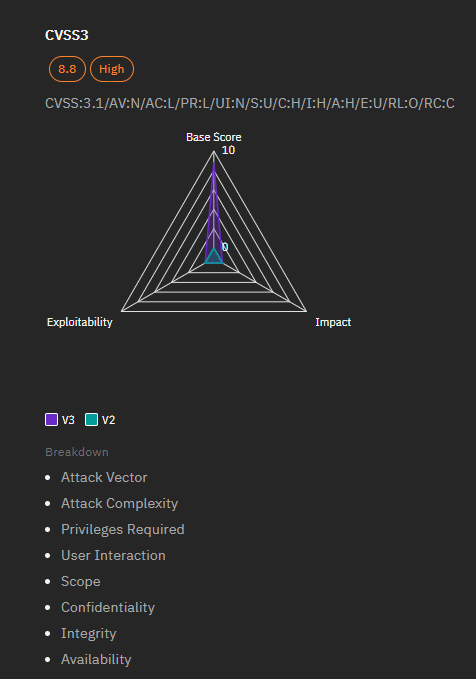
Attackers can exploit this vulnerability by leveraging access control weaknesses, potentially allowing them to read sensitive information, execute commands, and evade detection.
Immediate application of security updates provided by Microsoft is recommended to address this vulnerability and prevent potential exploitation.
For more details, refer to the Microsoft Security Response Center and the National Vulnerability Database.
CVE-2024-21416 is a Windows TCP/IP Remote Code Execution Vulnerability that allows attackers to execute arbitrary code on affected systems.
The vulnerability can be exploited through a heap overflow condition, allowing attackers to overwrite memory and execute arbitrary code without user interaction.
Microsoft has released security updates to address this vulnerability. Users are advised to apply these updates promptly to mitigate risks associated with potential exploitation.
For detailed information and references, users can consult the Microsoft Security Response Center and the National Vulnerability Database.
CVE-2024-38018 is a Remote Code Execution Vulnerability in Microsoft SharePoint Server, allowing attackers to execute arbitrary code on affected systems.
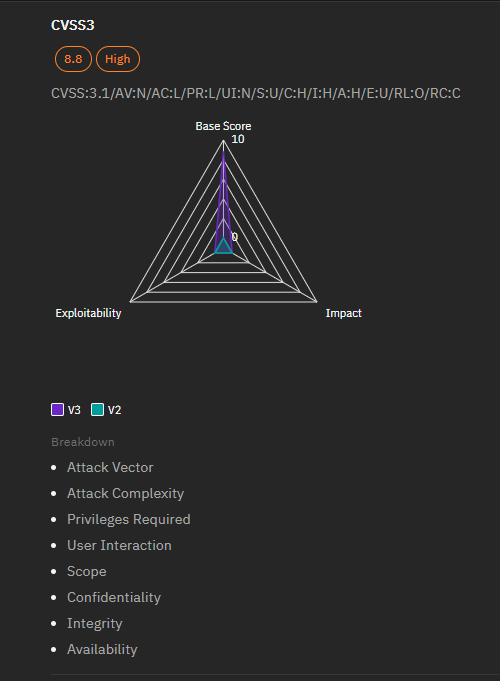
The vulnerability arises from the deserialization of untrusted data without adequate validation, which can be exploited remotely by authenticated users to execute arbitrary code on the server.
Microsoft has released security updates to address this vulnerability. Users are advised to apply these updates promptly to mitigate risks associated with this vulnerability.
The vulnerability was published on September 10, 2024, and updated shortly thereafter. The exploit prediction scoring system (EPSS) indicates a low probability of exploitation activity in the near term (0.05%) but highlights the need for immediate attention due to the potential impact.
These vulnerabilities highlight the importance of staying proactive and informed in the face of emerging threats. Whether you're patching systems or enhancing your defense strategies, addressing these CVEs swiftly is critical to maintaining security. For more detailed information on these CVEs and strategies to manage them effectively, explore how Strobes VI platform can help you stay ahead of the game.