Security Insights
Deep dives, expert analysis, and practical guidance on exposure management, adversarial validation, and the future of AI-driven exposure management.

Top 6 Data Breaches in July 2025 That Made Headlines
July 2025 was a turbulent month for cybersecurity, with several high-profile breaches exposing critical vulnerabilities across industries. From weak access controls to vendor mismanagement, these incidents underscored the need for a more robust, proactive security approach. Here's an in-depth look a

Top CVEs of July 2025: Exploits, Exposure, and the Risks
Some CVEs quietly fade into vendor advisories. Others don’t wait. The Top CVEs of July gained traction quickly - through public exploits, active scanning, or visibility in high-usage systems. This list isn’t built on CVSS alone. The Top CVEs of July were selected based on exploit availability, attac
EU Cyber Resilience Act: What You Must Do Before 2027
The European Union isn’t asking nicely anymore. With the Cyber Resilience Act, they’re laying down the law, literally, for how every company that makes or sells digital products in the EU must manage software security. And it's not a gentle nudge. It’s a full-scale regulatory revamp. From IoT to Saa
New CERT-In Guidelines 2025: What Every Security Team Needs to Act On Now
India just redrew the cybersecurity line in the sand. Until now, CERT-In’s mandates were mostly confined to government and critical infrastructure. That era is over. With the 2025 updates, these guidelines now apply to every business operating in India’s digital ecosystem. Whether you build software
The CEO’s Chronicles | Embracing The Pivot To CTEM When Others Doubted (Part 2)
"The biggest risk is not taking any risk... In a world that's changing quickly, the only strategy that is guaranteed to fail is not taking risks." - Mark Zuckerberg. Standing at the crossroads of cybersecurity evolution, I faced a decision that would define not just my career trajectory but potentia
Major Data Breach at Allianz Life: What Happened, Who Was Affected, and What You Can Do
Hackers have accessed personal information tied to most of the 1.4 million customers of Allianz Life Insurance Company of North America, according to a statement issued by its parent company. On July 16, 2025, a malicious threat actor gained access to a third-party cloud-based CRM system used by All

Strobes New Feature: Full Control Over Risk-Based Prioritization
Every security team knows the struggle: You've got hundreds (or thousands) of vulnerabilities, limited resources, and the constant question – "What should we fix first?" CVSS scores? They're a start, but they don't know that your payment processing system is more critical than your internal wiki. Tr

The CEO's Chronicles | When Nobody Believed - The 2022 Rejection Story (Part 1)
From Rejection to Recognition - The Strobes Journey The email was short. Brutal in its simplicity. It was the seventh rejection in three months. Seven different ways of hearing the same message: Nobody believes in your vision. As I sat in my office that evening in late 2022, staring at yet another p
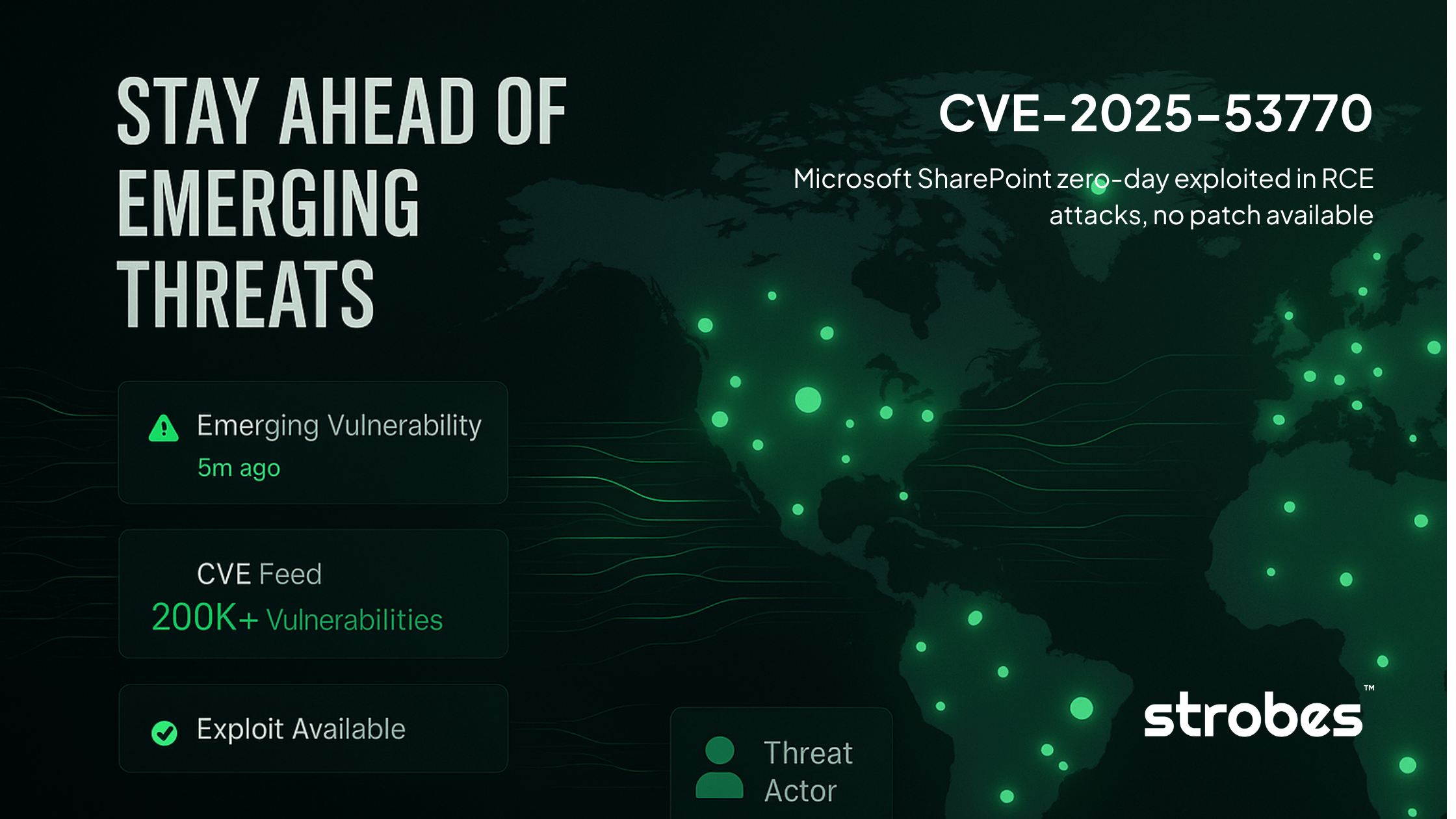
CVE-2025-53770 - Microsoft SharePoint zero-day exploited in RCE attacks
CVE-2025-53770 is a critical remote code execution vulnerability (CVSS 9.8) in on-premises Microsoft SharePoint Server that allows unauthenticated attackers to completely compromise servers through deserialization of untrusted data. The Microsoft SharePoint Zero-Day vulnerability is currently being

Why Attack Surface Analysis Must Be Your #1 Priority in 2025?
Enterprises today operate in environments where their digital footprint grows faster than their ability to secure it. As cloud adoption, API integrations, remote work, and third-party partnerships expand, attack surface analysis is now critical for gaining full visibility, uncovering hidden risks, a

Attack Surface Monitoring - Stop Chasing Alerts, Start Managing Risk
Modern enterprises are facing an unprecedented challenge, attack surfaces are growing faster than they can be secured. Without attack surface monitoring, cloud services, SaaS tools, third-party integrations, and remote work only accelerate this sprawl. A recent report found that 62% of organizations
Exposure Management vs Vulnerability Management - The Truth No One Tells You
Enterprises have poured time and resources into vulnerability management programs. Scanners sweep across networks and clouds, producing endless lists of issues to patch. On paper, this feels like control. In practice, teams are overwhelmed and attackers keep finding ways in. Vulnerability management