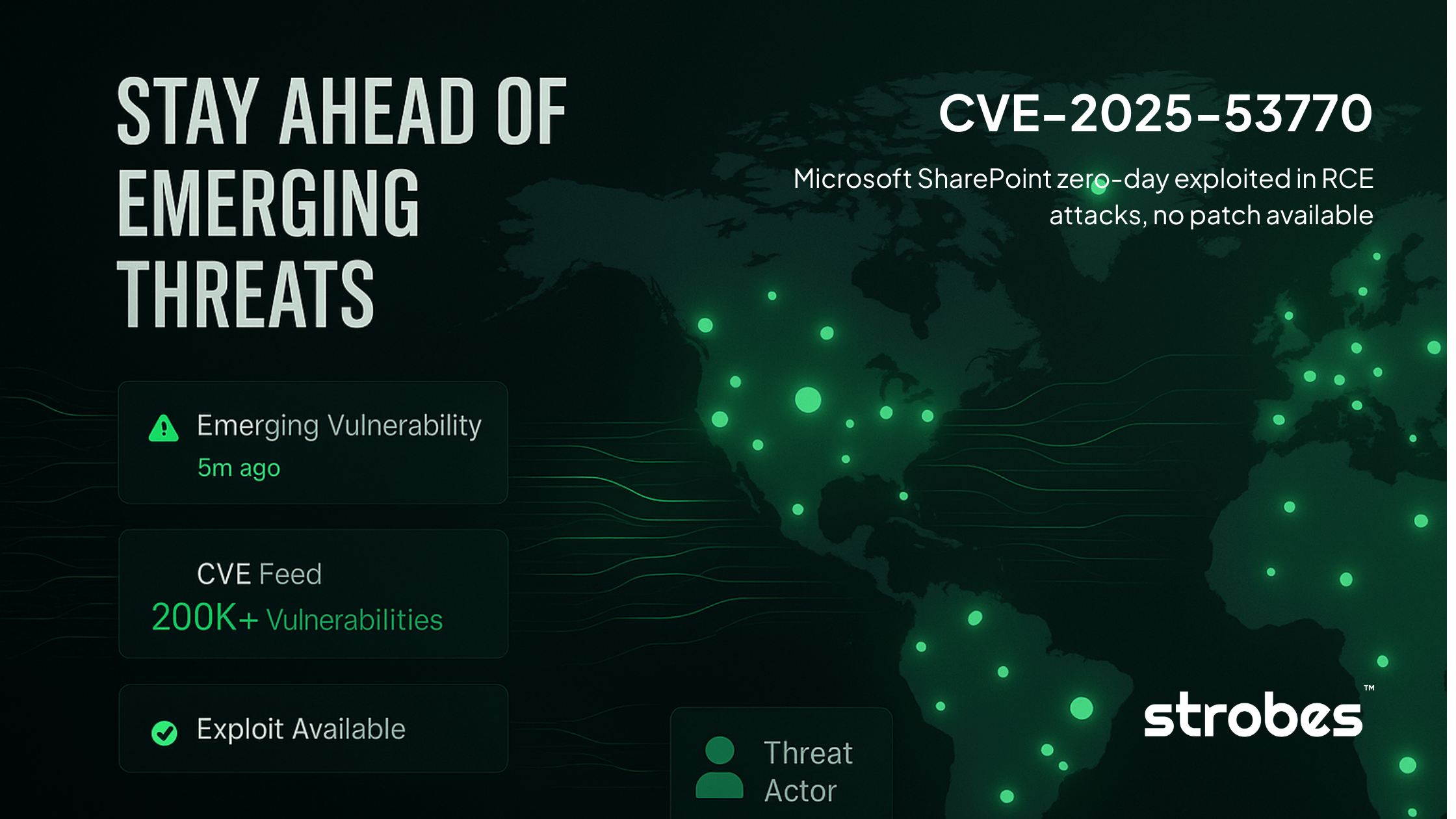
CVE-2025-53770 is a critical remote code execution vulnerability (CVSS 9.8) in on-premises Microsoft SharePoint Server that allows unauthenticated attackers to completely compromise servers through deserialization of untrusted data.
The Microsoft SharePoint Zero-Day vulnerability is currently being actively exploited in the wild with over 85 confirmed compromised servers globally since July 18, 2025. Most critically, no patches are available yet for SharePoint Server 2016 and 2019, making immediate mitigation essential.
The vulnerability enables attackers to steal SharePoint's cryptographic MachineKey configuration, granting persistent access even after eventual patching.
The SharePoint Zero-Day vulnerability represents a variant of the "ToolShell" exploit chain originally demonstrated at Pwn2Own Berlin 2025, weaponized within just 72 hours of public proof-of-concept disclosure. Organizations running on-premises SharePoint must take immediate action, as exploitation requires no authentication and can be automated at scale.
The root cause lies in SharePoint's ToolPane functionality, which improperly handles deserialization of untrusted data. Attackers can bypass authentication entirely by manipulating HTTP headers - specifically, setting the Referer header to /_layouts/SignOut.aspx when targeting the vulnerable /_layouts/15/ToolPane.aspx endpoint. This seemingly innocuous header tricks SharePoint into treating the request as legitimate, granting unauthenticated access to critical functionality.
The technical exploitation flow is devastatingly simple: An attacker sends a single HTTP POST request with the crafted Referer header, uploads a malicious .aspx file (typically named "spinstall0.aspx"), and this payload extracts the server's ValidationKey and DecryptionKey.
These cryptographic keys are SharePoint's crown jewels - with them, attackers can forge valid __VIEWSTATE payloads and maintain persistent access indefinitely.
The exploitation requires no user interaction, works against default SharePoint configurations, and has proven highly reliable in the wild. Security researchers have observed consistent success rates, with the attack complexity rated as "Low" in CVSS scoring. The simplicity explains the rapid adoption - within days of the initial public demonstration, threat actors had weaponized the vulnerability for mass exploitation campaigns.
The vulnerability's journey from legitimate security research to active exploitation illustrates the modern threat landscape's velocity. Dinh Ho Anh Khoa from Viettel Cyber Security originally discovered the ToolShell vulnerabilities, demonstrating them at Pwn2Own Berlin 2025 in May and earning a $100,000 prize. Microsoft patched these initial vulnerabilities (CVE-2025-49704 and CVE-2025-49706) on July 8, 2025.
However, on July 14, security firm CODE WHITE GmbH publicly demonstrated they had reproduced the ToolShell exploit chain, posting proof-of-concept screenshots on social media.
This public disclosure appears to have triggered immediate threat actor interest. By July 18 at 18:00 CET, Eye Security detected the first wave of active exploitation targeting their customers' SharePoint servers from IP address 107.191.58.76.
The timeline from public PoC to mass exploitation was just 72 hours. A second wave followed on July 19 from IP 104.238.159.149, prompting Eye Security to publish their findings and Microsoft to assign CVE-2025-53770 as a variant of the original vulnerabilities. CISA added it to their Known Exploited Vulnerabilities catalog on July 20, mandating federal agencies implement mitigations within 24 hours.
The vulnerability affects all on-premises SharePoint Server deployments:
SharePoint Online (Microsoft 365) is not affected. This distinction is crucial - only organizations running SharePoint on their own infrastructure face this threat. Shadowserver Foundation identified approximately 9,300 publicly accessible SharePoint servers worldwide that could be potential targets.
The patch availability creates a critical gap. While SharePoint Subscription Edition users can apply security updates immediately, organizations running the widely-deployed 2016 and 2019 versions must rely entirely on mitigations. Microsoft has confirmed they're developing patches but hasn't provided a timeline, leaving a significant portion of the SharePoint ecosystem exposed.
Organizations can detect exploitation through several clear indicators. The primary indicator is creation of a file named "spinstall0.aspx" in SharePoint layout directories, with SHA256 hash 92bb4ddb98eeaf11fc15bb32e71d0a63256a0ed826a03ba293ce3a8bf057a514. This file contains the payload that extracts cryptographic keys.
Network-level indicators include POST requests to /_layouts/15/ToolPane.aspx?DisplayMode=Edit&a=/ToolPane.aspx with the Referer header set to /_layouts/SignOut.aspx. The attacking infrastructure has used consistent patterns, including the User-Agent string Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0.
For organizations using Microsoft 365 Defender, specific KQL queries can identify compromise:
DeviceFileEvents
| where FolderPath has_any (@'microsoft shared\Web Server Extensions\16\TEMPLATE\LAYOUTS')
| where FileName has "spinstall0"Additional behavioral indicators include w3wp.exe processes spawning encoded PowerShell commands and unusual outbound connections from SharePoint servers. The known malicious IP addresses (107.191.58.76, 104.238.159.149, 96.9.125.147) should be blocked immediately.
With no patches available for most versions, enabling Antimalware Scan Interface (AMSI) integration is the critical first mitigation step. AMSI integration, available since SharePoint's September 2023 security updates, allows Microsoft Defender Antivirus to inspect and block malicious payloads during execution. Organizations must install Microsoft Defender Antivirus on all SharePoint servers to enable this protection.
If AMSI cannot be enabled, Microsoft recommends immediately disconnecting SharePoint servers from the internet. This drastic measure reflects the severity - unprotected internet-facing servers will likely be compromised within hours given the ongoing mass exploitation campaigns.
After implementing AMSI or patching, organizations must rotate their SharePoint machine keys. The stolen cryptographic material allows attackers to maintain access even after patching. Use PowerShell's Update-SPMachineKey cmdlet or SharePoint Central Administration's Machine Key Rotation Job, followed by an IIS reset on all servers.
Additional hardening includes implementing Web Application Firewall rules to block suspicious ToolPane requests, enabling comprehensive logging for forensic analysis, and preparing incident response procedures. Organizations should audit all SharePoint layout directories for unauthorized files and review authentication logs for anomalies.
CVE-2025-53770 represents more than a typical vulnerability - it's a systemic breakdown in SharePoint's security architecture that enables persistent compromise. The theft of cryptographic keys means that even after patching, attackers who successfully exploited the vulnerability retain the ability to forge valid requests.
This necessitates comprehensive post-compromise actions including full credential rotation, security token invalidation, and potentially complete server rebuilds.
The rapid weaponization timeline - from public PoC to mass exploitation in 72 hours - demonstrates how quickly the threat landscape evolves. Organizations can no longer rely on traditional patch cycles when zero-days can be operationalized within days.
This incident underscores the critical importance of defense-in-depth strategies, including network segmentation, endpoint detection, and rapid incident response capabilities.
For the broader security community, CVE-2025-53770 serves as a cautionary tale about responsible disclosure. While the original Pwn2Own research followed proper channels, the subsequent public reproduction of the exploit appears to have directly enabled mass exploitation. The security research community must balance transparency with the potential for immediate weaponization.
Organizations running on-premises SharePoint must act immediately:
The combination of critical severity (CVSS 9.8), active exploitation, authentication bypass, and the ability to establish persistence makes CVE-2025-53770 one of the most dangerous SharePoint vulnerabilities in recent years.
With confirmed compromises continuing to grow and no timeline for patches on older versions, organizations cannot afford to delay mitigation of risks efforts. The window for preventive action is rapidly closing as threat actors continue scanning for vulnerable servers worldwide.
Additional Resources: