Like every year, we are releasing some research and analysis around our pen-testing in 2023. This article covers key penetration testing statistics, including what category of vulnerabilities we commonly report across hundreds of customers, and how we reduce compliance times and turnaround time when reporting critical vulnerabilities.
In a different article, we will also share some research on how our red teaming and app sec teams found clever ways to exploit vulnerabilities and provide strong value to our customers.
Our exploration begins by charting the trajectory of assessment volumes, offering a panoramic view of how different sectors and geographic locations grapple with the ever-present specter of cyber threats. As we dive deeper, we confront the fading allure of low-hanging fruits — vulnerabilities that were once exploited with ease — and examine the reasons behind their gradual decline.
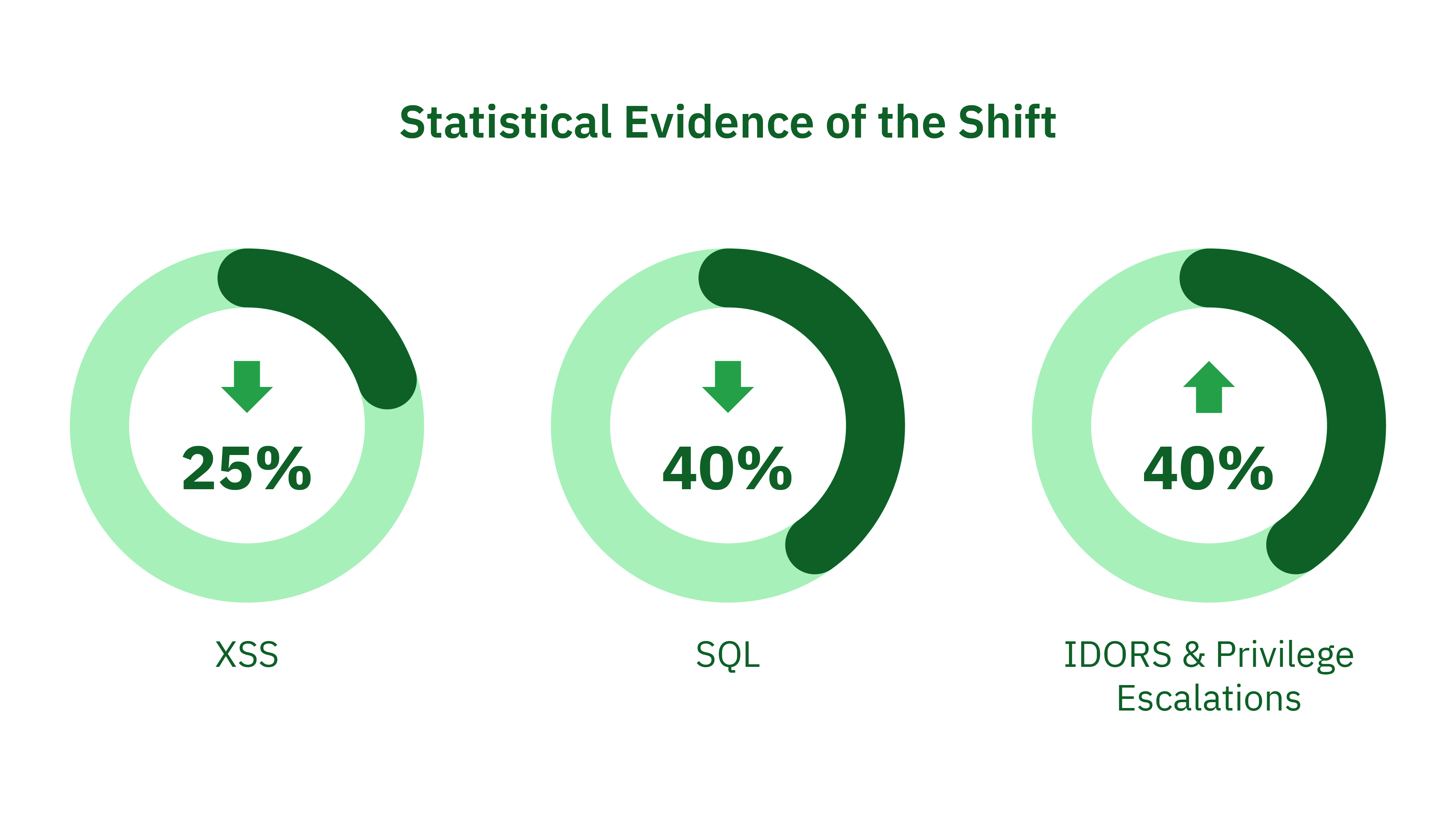
Complementing our qualitative analysis, we present compelling statistical evidence that substantiates the paradigm shift in cybersecurity.
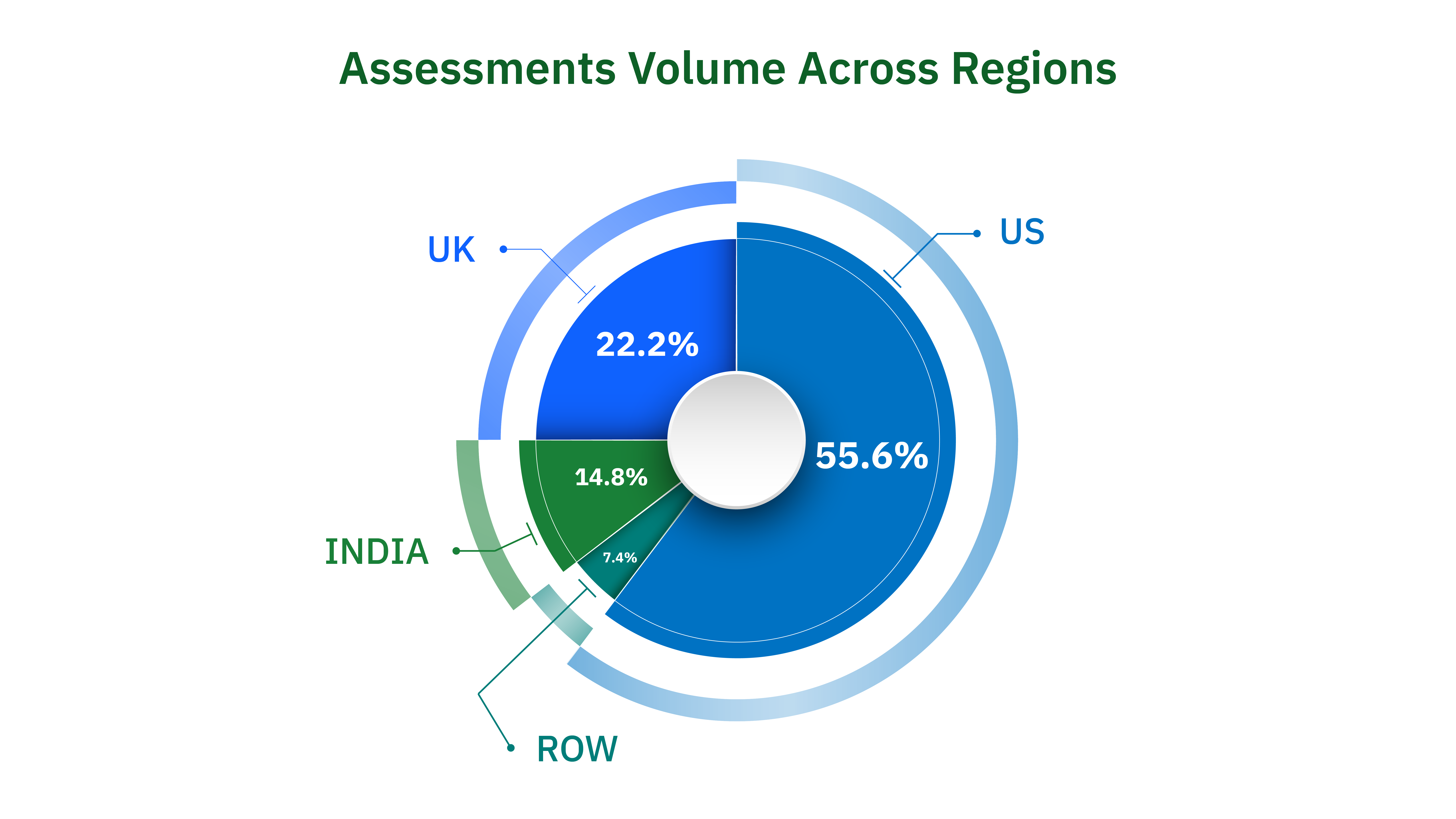
In 2023, we have worked with well over 150 customers, starting from startups to enterprises with over 10,000 employees. Again, these customers fall under different industries like Internet, Banking, Fintech, E-commerce, AI, Blockchain and more. We have seen some crazy trends in industries like banking, financial services, and AI.
Banking & Finance was leading from the front in terms of volume for pen-testing, especially in markets like the US, Europe, and India. India, driven by strict RBI regulations, showed strong penetration testing statistics, with companies required to conduct regular pentests. Even businesses registered outside India but looking to operate there had to meet these testing requirements consistently.
From a European standpoint, the GDPR data policies are still going strong, and we see a similar trend from them, more and more companies want to perform pen-testing.
Here is the volume of assessments across industries, assessments include IP or application testing:
In the rapidly evolving world of cybersecurity, the trends and vulnerabilities witnessed in penetration testing (pentesting) reflect the changing dynamics of web applications and their security postures.
As we analyse our data from 2023, a notable trend emerges: the gradual decline of traditional vulnerabilities like Cross-Site Scripting (XSS) and SQL Injection, contrasted by the rise in complex issues such as Privilege Escalations, Insecure Direct Object References (IDORs), Server-Side Request Forgery (SSRF), business logic errors, and Server-Side Template Injection (SSTI). This article delves into this shift, shedding light on the reasons behind it and its implications on the cybersecurity landscape.
Historically, XSS and SQL Injection have been the 'low-hanging fruits' of web application vulnerabilities. Easy to identify and exploit, these vulnerabilities have been the bane of web applications for years. XSS, for instance, has been a prevalent issue, allowing attackers to inject malicious scripts into web pages viewed by other users.
SQL Injection, on the other hand, has enabled attackers to manipulate back-end databases through poorly designed web applications. However, our data indicates a significant downturn in these vulnerabilities. A key reason is the advancement in development frameworks and technologies. Modern frameworks like Next.js, React, and Django have built-in security features that effectively neutralise such threats.
For instance, React's DOM sanitization automatically mitigates the risk of XSS attacks. Similarly, ORMs (Object-Relational Mapping) used in frameworks like Django provide a layer of protection against SQL Injection by handling data queries securely.
Also Read: CVE-2025-29927 – Understanding the Next.js Middleware Vulnerability
While the traditional vulnerabilities are on the decline, we are witnessing an uptick in more sophisticated security challenges. Privilege escalation attacks, which involve gaining unauthorised access to higher-level permissions, are becoming more common. These attacks exploit flaws in application logic or system configurations and are often harder to detect and prevent.
IDORs and SSRF present similar challenges. IDORs exploit the way web applications manage data, allowing attackers unauthorised access to data belonging to other users. SSRF attacks trick a server into performing requests on behalf of the attacker, potentially leading to sensitive data exposure.
Business logic errors, often overlooked in automated testing, are becoming a significant threat. These errors arise from flawed application logic and can lead to unauthorised actions or data exposure. SSTI, meanwhile, targets the way web applications process templates, enabling attackers to inject malicious code into a server-side template, leading to data exposure or server compromise.
The shift in the vulnerability landscape is also attributable to modern development practices. Applications developed within the last five years, particularly those using newer frameworks and technologies, are less prone to traditional vulnerabilities. These applications are designed with security as a core principle, incorporating secure coding practices from the outset.
Frameworks like Next.js and React enforce secure defaults and encourage patterns that reduce the risk of common vulnerabilities. Additionally, the adoption of DevSecOps practices, where security is integrated into the development life cycle, has played a crucial role in enhancing application security.
Also Read: Open Source Security: How Strobes Integrates Security into Your Dev Workflow
To substantiate these observations, let's turn to some statistics. According to our data, XSS vulnerabilities have seen a reduction of approximately 25% in modern web applications compared to those developed five years ago. Similarly, SQL Injection vulnerabilities have decreased by around 40% in newer applications. On the other hand, issues like Privilege Escalations and IDORs have seen an increase of about 40% in the same period.
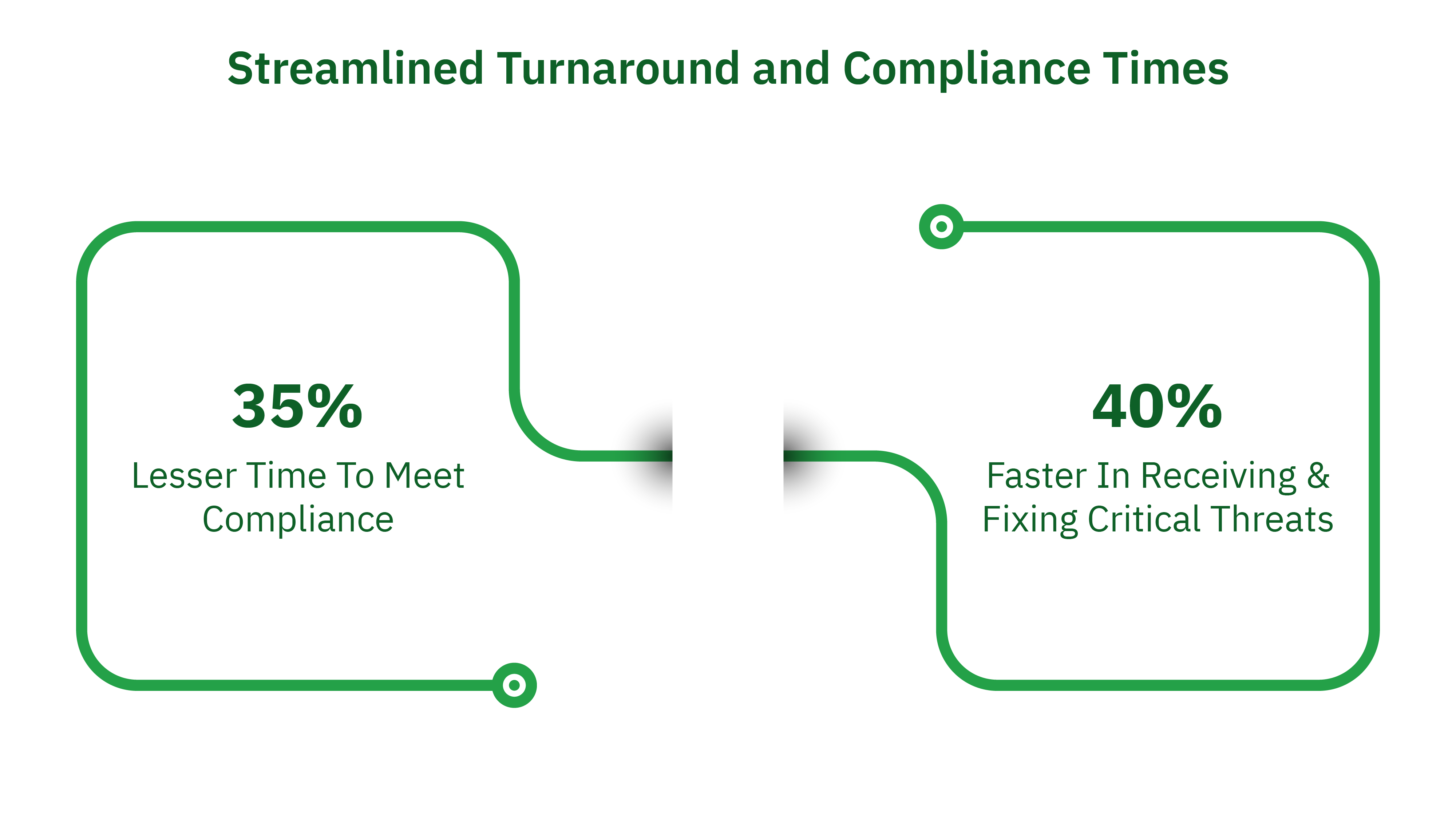
The agility of Strobes PTaaS is evident in its turnaround times. Over the past year, our platform and team have facilitated a 40% reduction in the time-to-remediation for critical vulnerabilities, a benchmark that significantly outpaces the industry average. By implementing integrated workflows and prioritised issue tracking, customers have reported a 35% improvement in their time-to-compliance, ensuring they meet regulatory standards swiftly without compromising on thoroughness.
For example, one of the customers using our Strobes PTaaS platform requested an urgent application pen-test ahead of a critical audit. The audit was time-sensitive and could have delayed their deal with a client. Strobes delivered the pentest report within 48 hours of starting the test, without compromising on quality or coverage. Our penetration testing statistics reflect how often we meet fast turnaround needs like this while maintaining depth and accuracy.
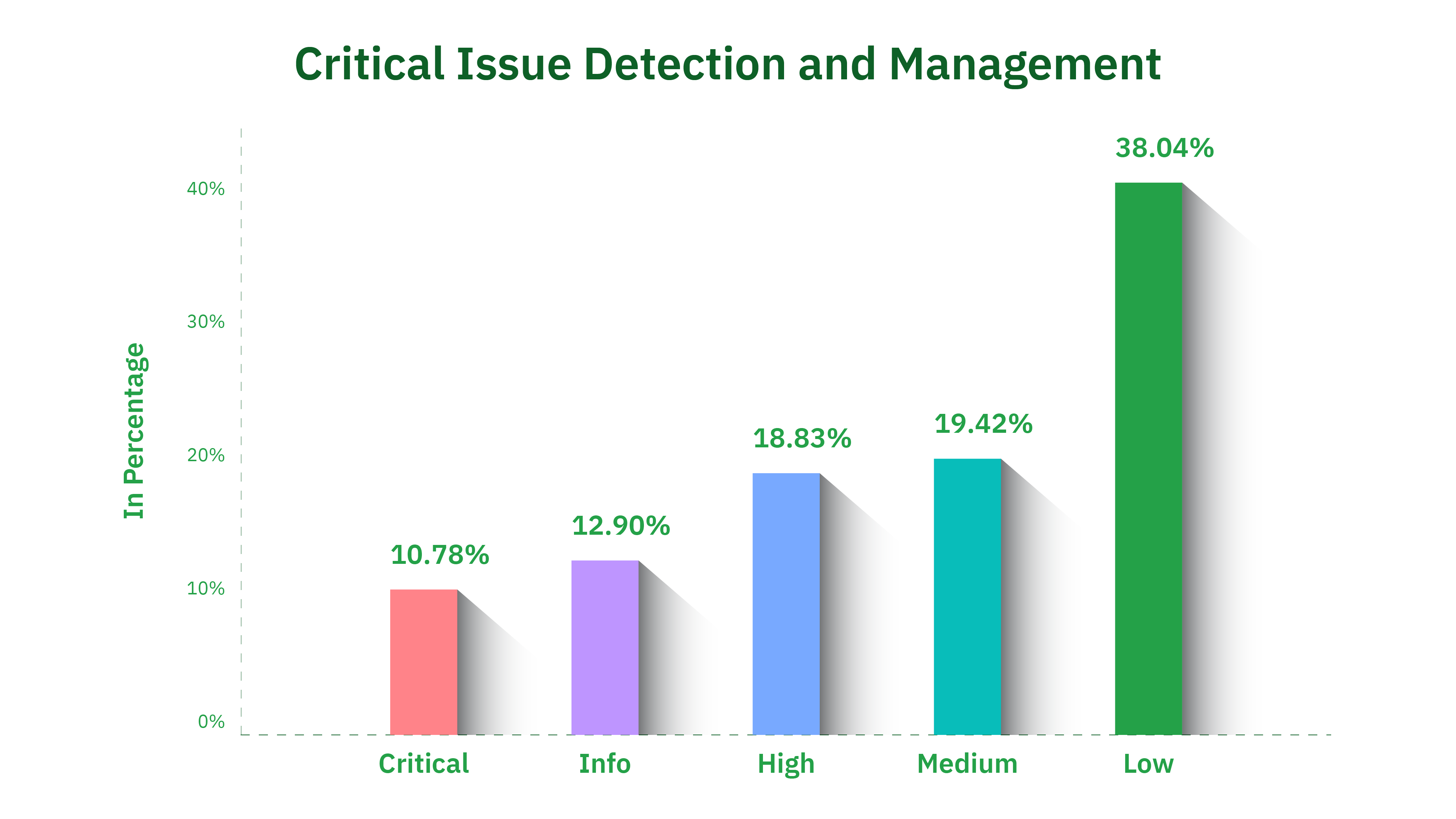
Critical issue detection is at the heart of Strobes PTaaS's efficacy. In 2023, our team identified and helped remediate of over 700 critical vulnerabilities across applications, networks and the cloud. The critical vulnerabilities are really critical and could have allowed a bad actor to compromise the customer’s infrastructure or even exfiltrate PII information.
Our approach is tailored and nuanced, cognizant of the unique challenges each industry faces:
Further to the aforementioned industries, our pentesting services have made significant inroads in other sectors:
Strobes' approach to Pentesting as a Service (PTaaS) is transforming traditional penetration testing practices, enhancing customer satisfaction through several innovative features. Here's an exploration of how Strobes is achieving this:
The picture is clear. Strobes PTaaS is not just another cybersecurity platform; it’s a strategic partner in the cybersecurity ecosystem. By delivering tailored solutions, reducing remediation times, and enhancing compliance efficiency, we empower businesses to stay ahead of security threats.
Our penetration testing statistics from 2023 back this up, showing how our approach improves detection, reporting, and overall security outcomes across industries. Request a demo to see how Strobes can strengthen your security program.
Related Reads: